Foundations of Security Week2 Seminar: Ethical Hacking Phases
272 字
1 分钟
Foundations of Security Week2 Seminar: Ethical Hacking Phases

Practical Session Plan: Ethical Hacking Phases
Objective:
To introduce you to ethical hacking by performing basic tasks related to the phases in a controlled environment.
Phases of Ethical Hacking Continue…
Ethical hacking is distributed into six different phases.
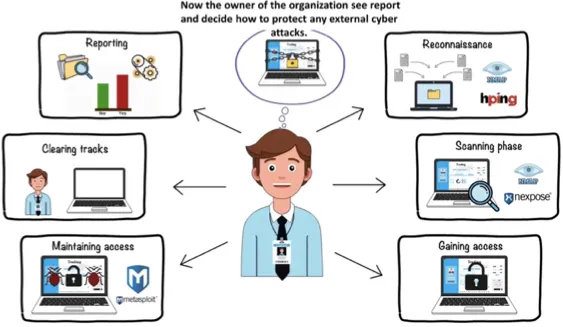
Phase 1: Reconnaissance
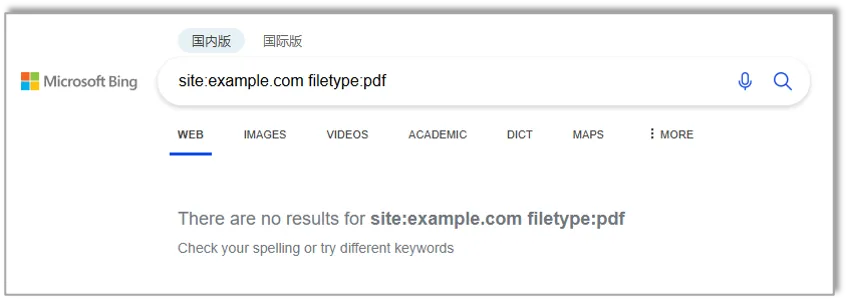
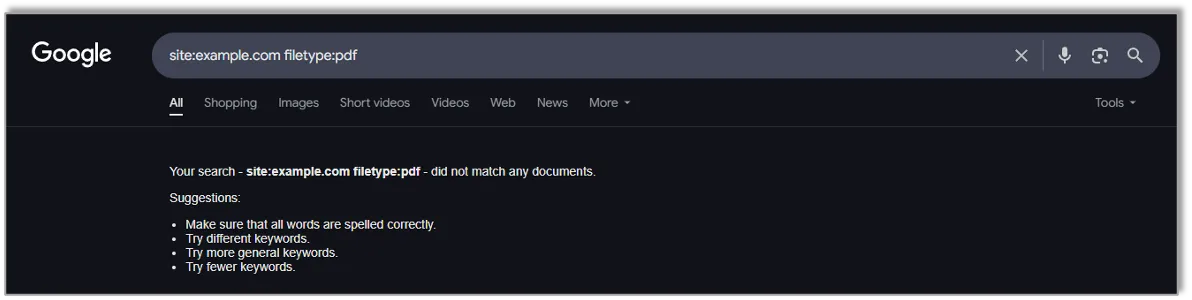
Task1: Perform passive information gathering
- Open your web browser and in your search engine (eg www.bing.com) search for
site:example.com filetype:pdf - Replace
example.comwith an actual website.
  |  |
|---|
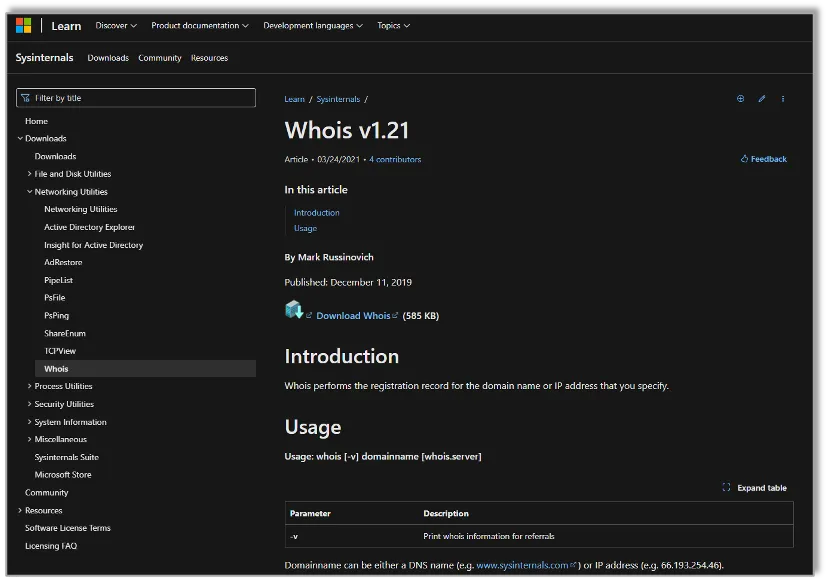
Task2: Perform passive information gathering with Whois Lookup
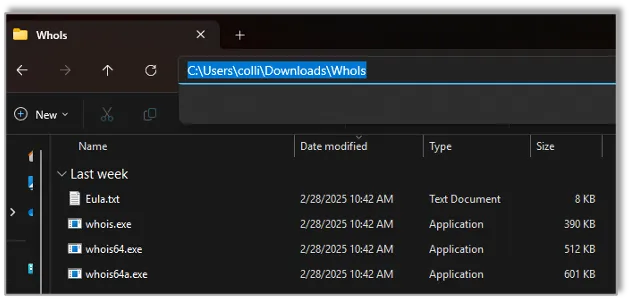
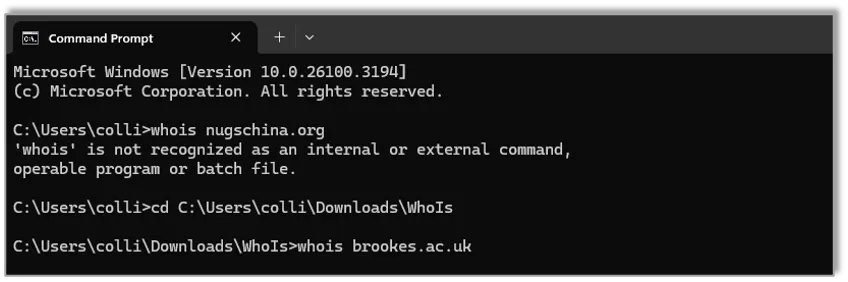
- Download whois from this link https://learn.microsoft.com/en-us/sysinternals/downloads/whois
- Extract the zip file
- Open Command Prompt and navigate to (
cd C:\Users\colli\Downloads\WhoIs) the directory of the extracted - Type
whois brookes.ac.uk
| 1 | 2 | 3-4 |
|---|---|---|
 |  |  |
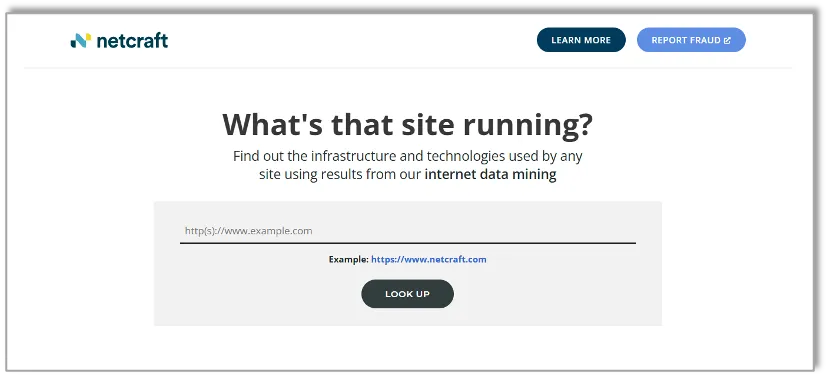
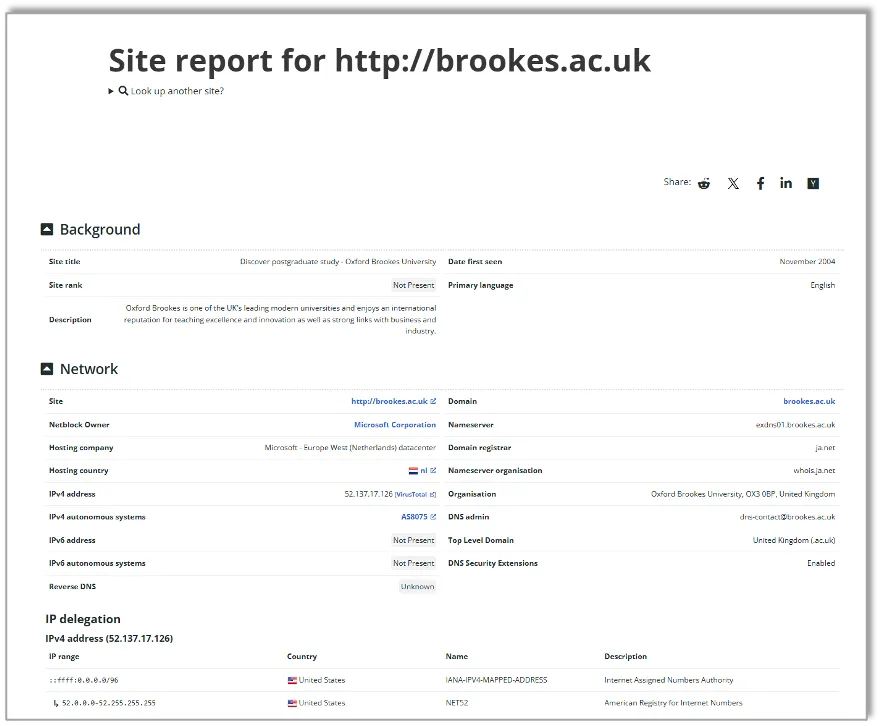
Task3: Perform passive information gathering with online tool Netcraft
- Go to https://sitereport.netcraft.com
- Type
brookes.ac.uk
| 1 | 2 |
|---|---|
 |  |
Phase 2: Scanning
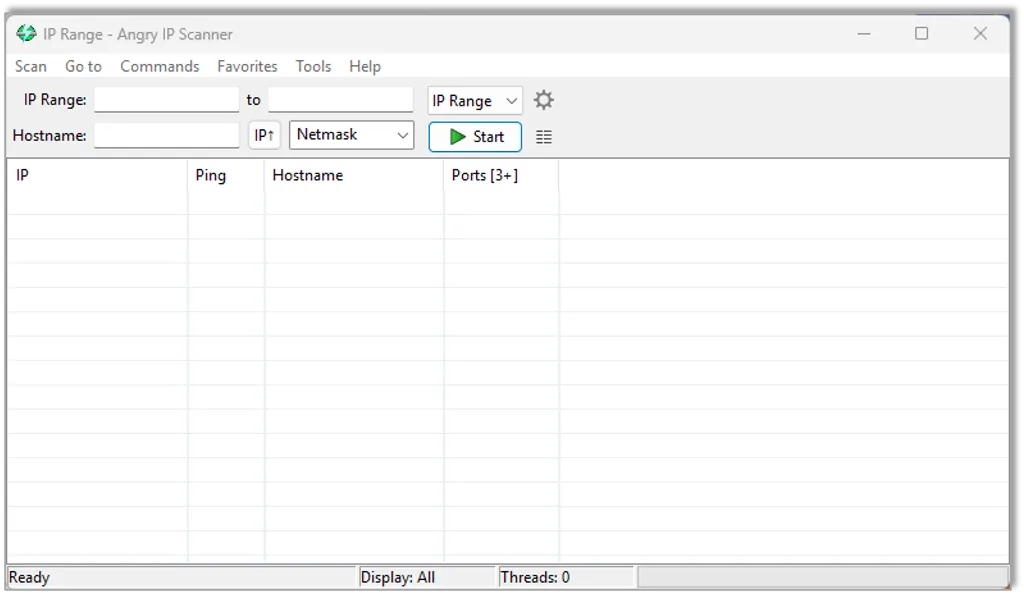
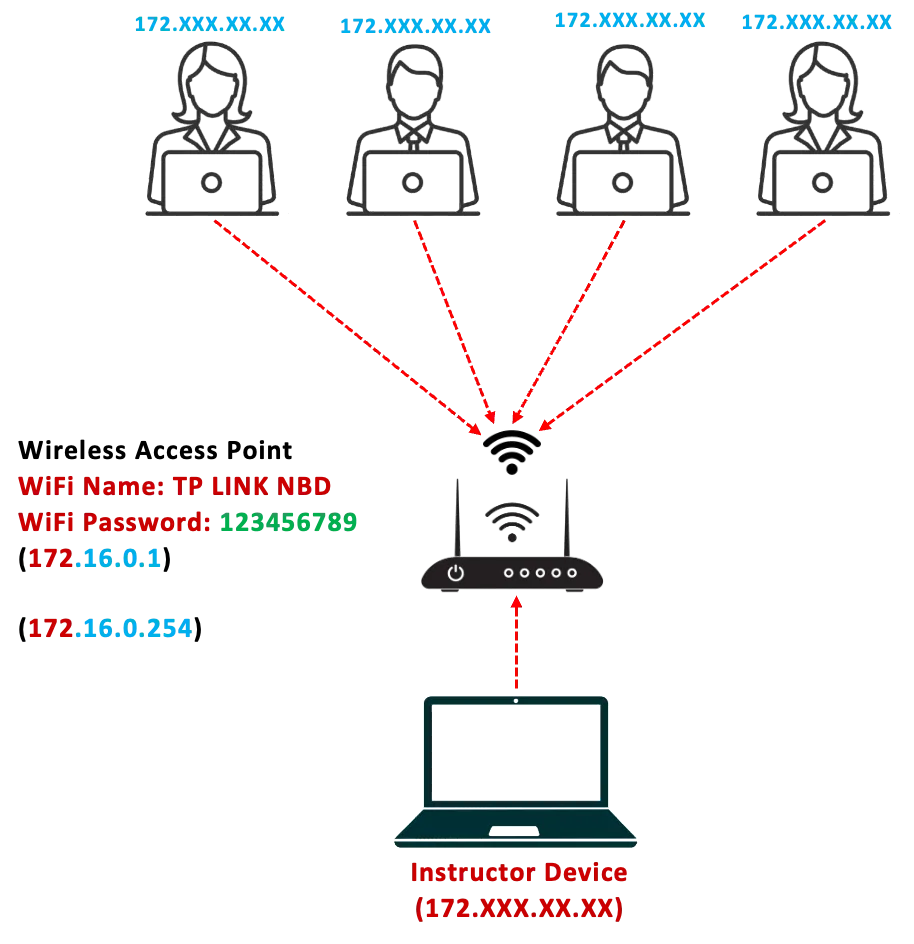
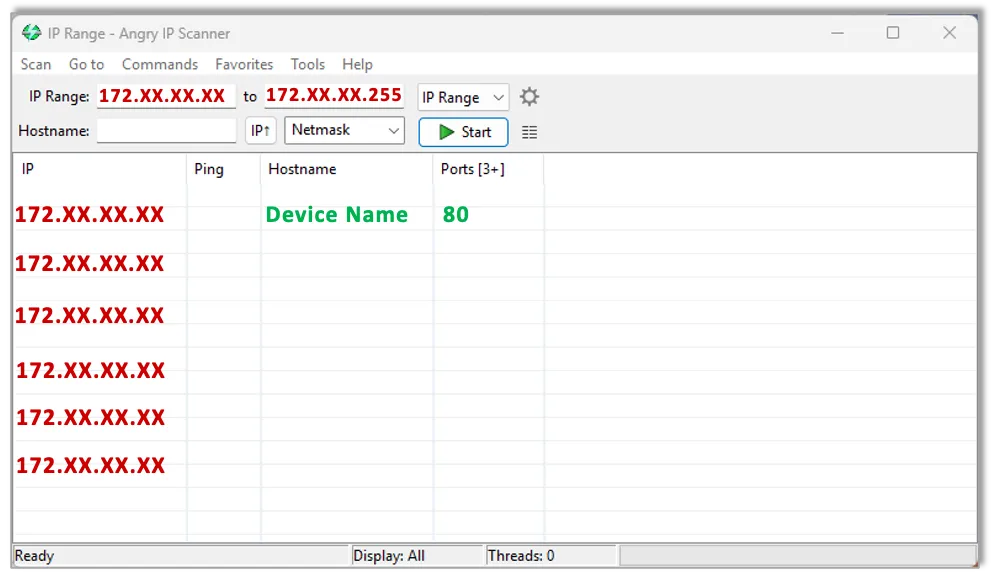
Task4: Scan for open ports and vulnerabilities
- a. Download and Install Angry IP Scanner from https://angryip.org/download
| Angry IP Scanner |  |
|---|
- Scan local devices for open ports and vulnerabilities.
- Find the device with IP address 192.168.1.XX in the list
 |  |
|---|
Phase 3: Gaining Access (File Services)
Task5: Attempt access public folder or login using weak credentials
- Attempt to gain access to the public folder of the device with IP address
\\192.168.XX.XXin your previous task. - Attempt to gain access to the computer as a user using a weak password
| 1 | 2 |
|---|---|
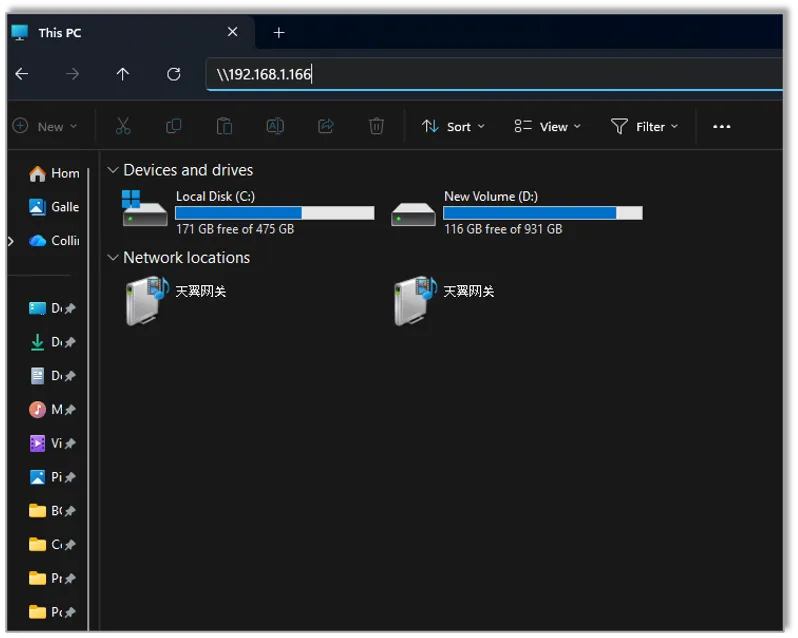 | 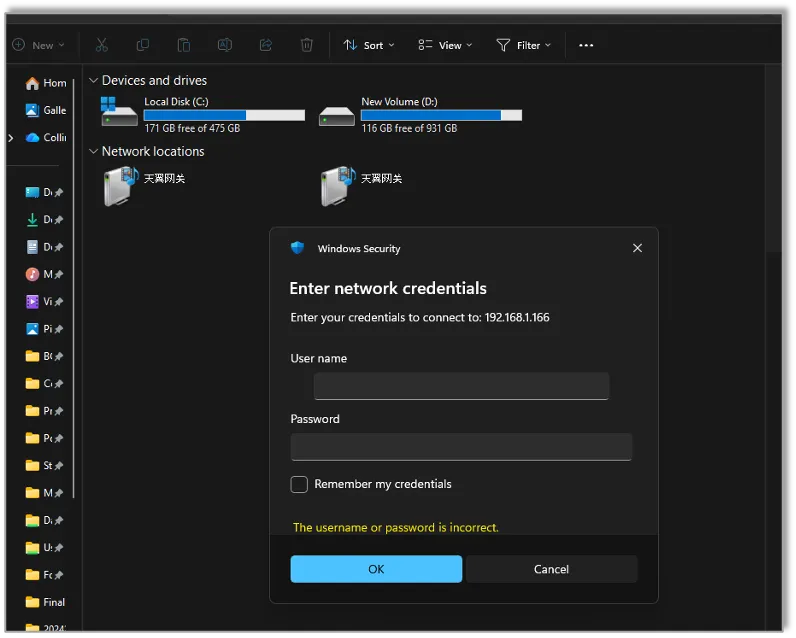 |
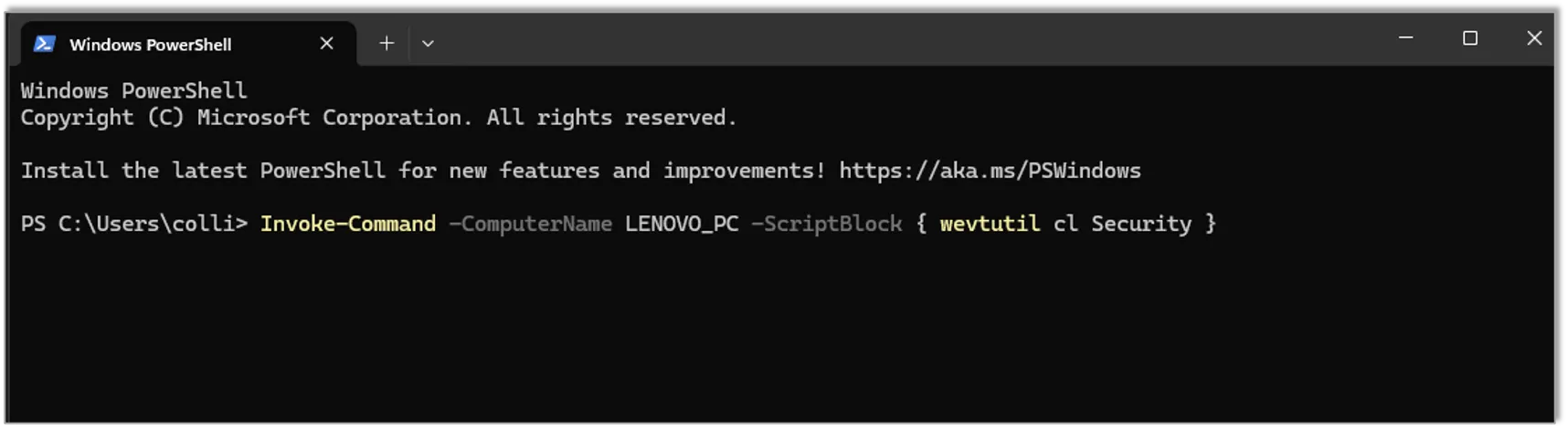
Phase 5: Clearing Tracks
Task5: Clear the Security event logs
If you have been able to gain admin access, Open PowerShell on your machine and run:
Invoke-Command -ComputerName TARGET_PC -ScriptBlock { wevtutil cl Security }(Replace TARGET_PC with the real hostname or IP.)
Phase 6: Reporting
Task6: Document findings
Create a simple report using:
- Screenshots of scans.
- A list of open ports and possible vulnerabilities.
- Security recommendations.
Gaining Access: (Web Services and Web Data)
Our next session will explore gaining access via web services
| SQL Injection |
|---|
 |
支持与分享
如果这篇文章对你有帮助,欢迎分享给更多人或赞助支持!
Foundations of Security Week2 Seminar: Ethical Hacking Phases
https://firefly.anka2.top/posts/obu/level5/semester2/fos/week2/seminar/ 相关文章 智能推荐
1
Foundations of Security Week8 Seminar: Digital Signature
Foundations of Security A digital signature is a cryptographic result attached to data that helps a receiver verify three things: Who sent it, It was not changed, Sender cannot easily deny it
2
Foundations of Security Week8 Lecture
Foundations of Security Data Encryption Standard (DES) algorithm
3
Foundations of Security Week7 Seminar: Password Cracking & Secure Hashing
Foundations of Security Generate & Compare Hashes, Rainbow Tables, Hashing vs Encryption, Dictionary Attack, Salting
4
Foundations of Security Week7 Lecture
Foundations of Security Diffie–Hellman key exchange, ElGamal encryption, Digital signature, RSA signature, Feistel cipher
5
Foundations of Security Week6 Seminar: Phishing
Foundations of Security Understanding and Defending Against Social Engineering Attacks.
随机文章 随机推荐
