Foundations of Security Week7 Lecture

Lecture Outline
- Limitations of symmetric key encryption
- Introduction to Diffie–Hellman key exchange
- Introduction to ElGamal encryption
- Key generation, encryption and decryption process of ElGamal
- Introduction to Digital signature and RSA signature
- Structure of the Feistel cipher
Learning Outcomes
By the end of this lecture, students should be able to:
- Explain the key distribution problem in symmetric encryption
- Describe the purpose of the Diffie–Hellman key exchange
- Explain how two parties establish a shared secret using Diffie–Hellman
- Apply ElGamal encryption through practical examples
- Understand Digital Signature and How the RSA signature works
- Describe the structure and working principle of the Feistel cipher
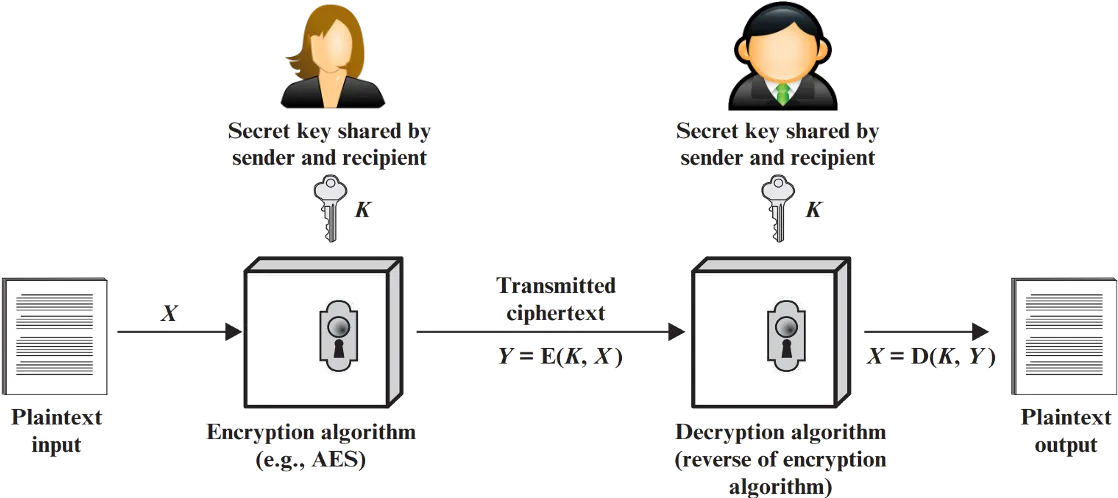
Symmetric Key Encryption
Symmetric Key Encryption is a cryptographic method where the same key is used for both encryption and decryption.
In this system, both the sender and the receiver share a secret key, and they use it to transform plaintext (original message) into ciphertext (encrypted message) and vice versa.
Problem with the Symmetric Key Encryption
Symmetric Key Encryption
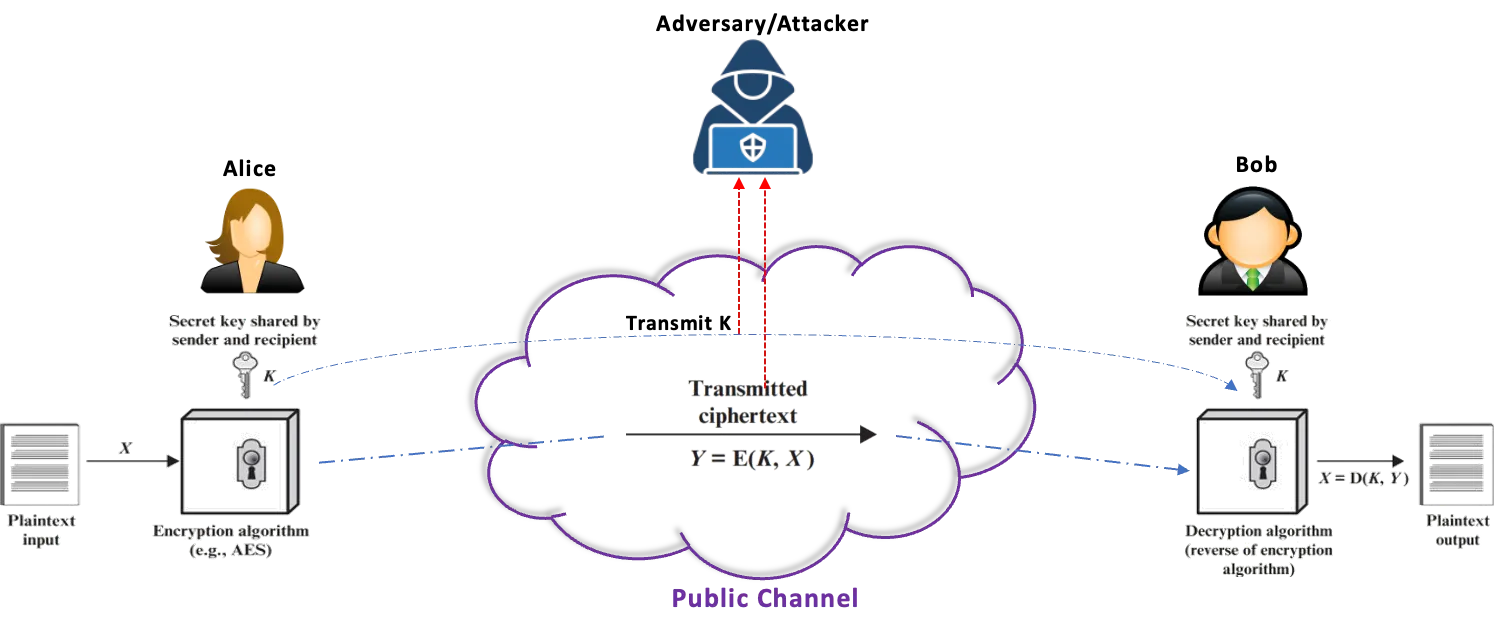
Problem with the Symmetric Key Encryption
- Transmission of secret key over a public channel is vulnerable to attacks.
- Attacker can intercept both the shared secret key (K) and ciphertext during transmission.
- If the secret key is compromised, all communication using that key is at risk.
Diffie-Hellman Key Exchange
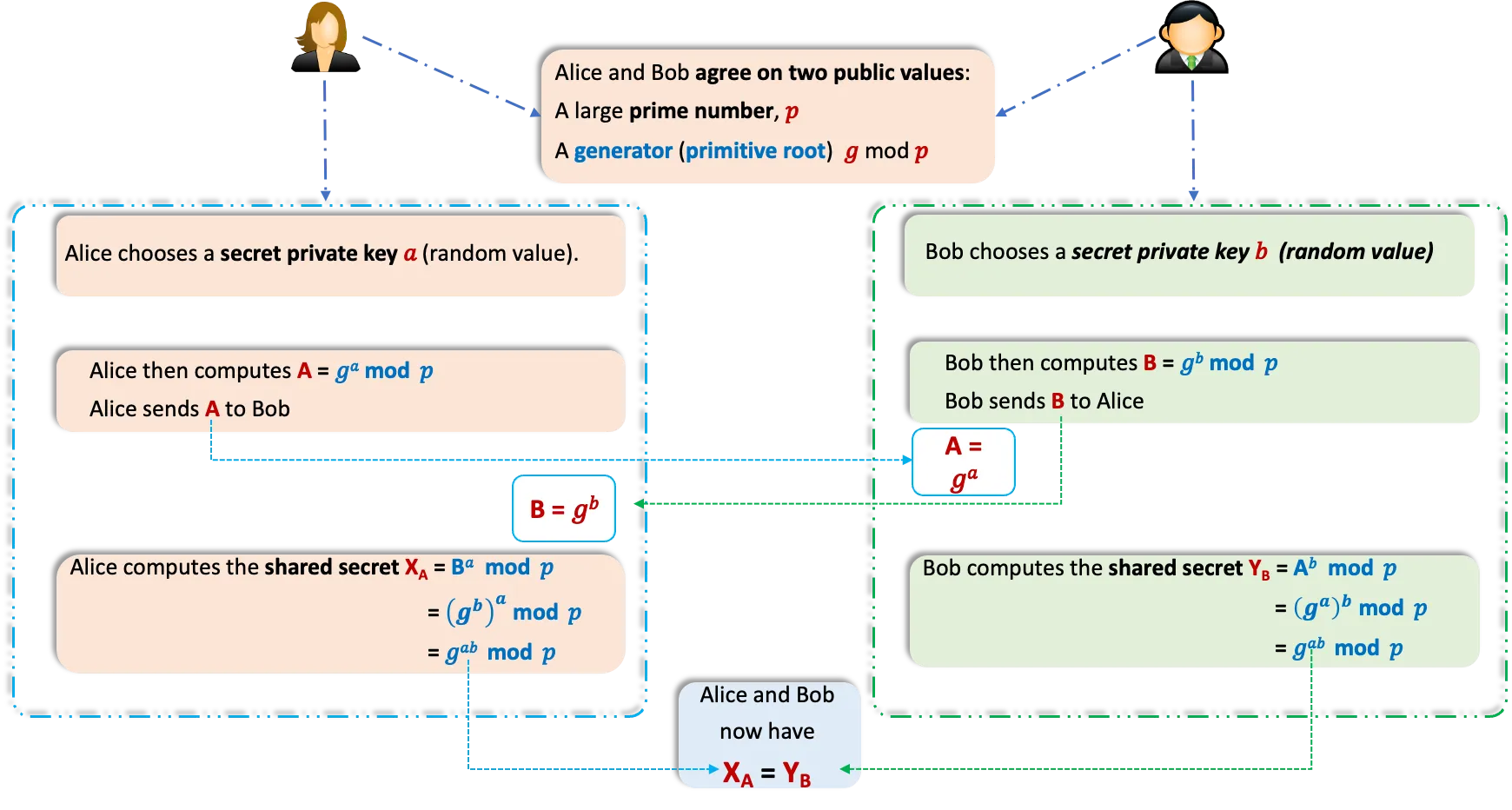
- The Diffie–Hellman key exchange is a method for securely exchanging cryptographic keys over a public channel. It allows two parties to each generate a shared secret key without directly transmitting it over the network.
- Introduced in 1976 by Whitfield Diffie and Martin Hellman.
- It was the first practical method for establishing a shared secret over an unprotected communications channel.
- It allows two parties who have never met before to securely establish a shared key, which can then be used to secure their communication.
- It enables secure key exchange without transmitting the actual secret key
How it works
Reading Assignment
How to find a generator/primitive root
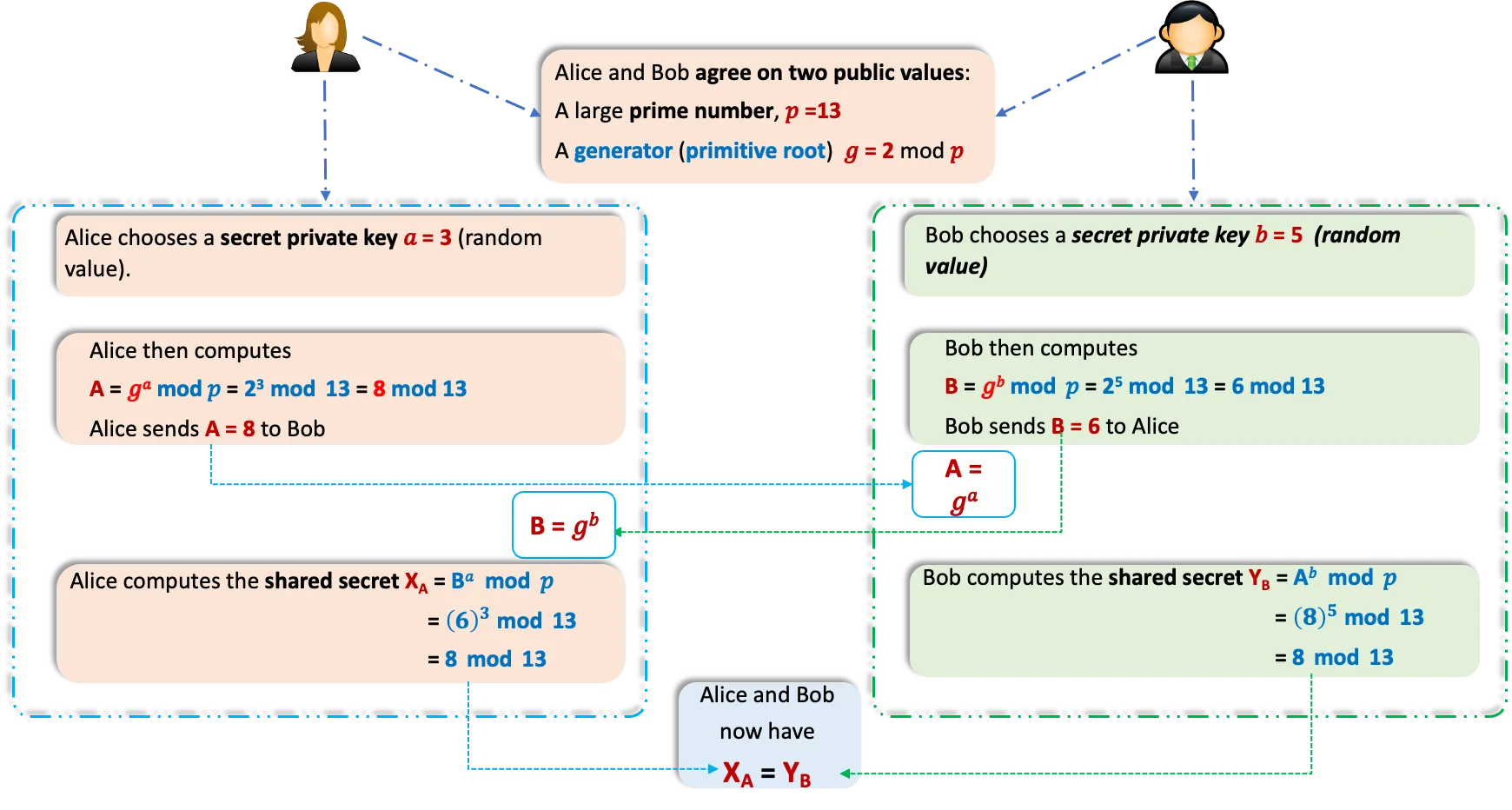
Example
Quiz
 |  |
|---|---|
| Alice’s secret key: | Bob’s secret key: |
Task:
Users A and B are using the Diffie-Hellman key exchange method with a common prime and a generator . User A chooses her secret key and computes her public value , which she sends to User B through the public channel. User B selects his secret key and computes his public value , which he sends to User A through the public channel. What is the common secret key shared between User A and User B?
ElGamal Encryption
The ElGamal Encryption Algorithm is a public-key cryptosystem based on the difficulty of the discrete logarithm problem. It was developed by Taher ElGamal in 1985 and is used for secure data transmission.
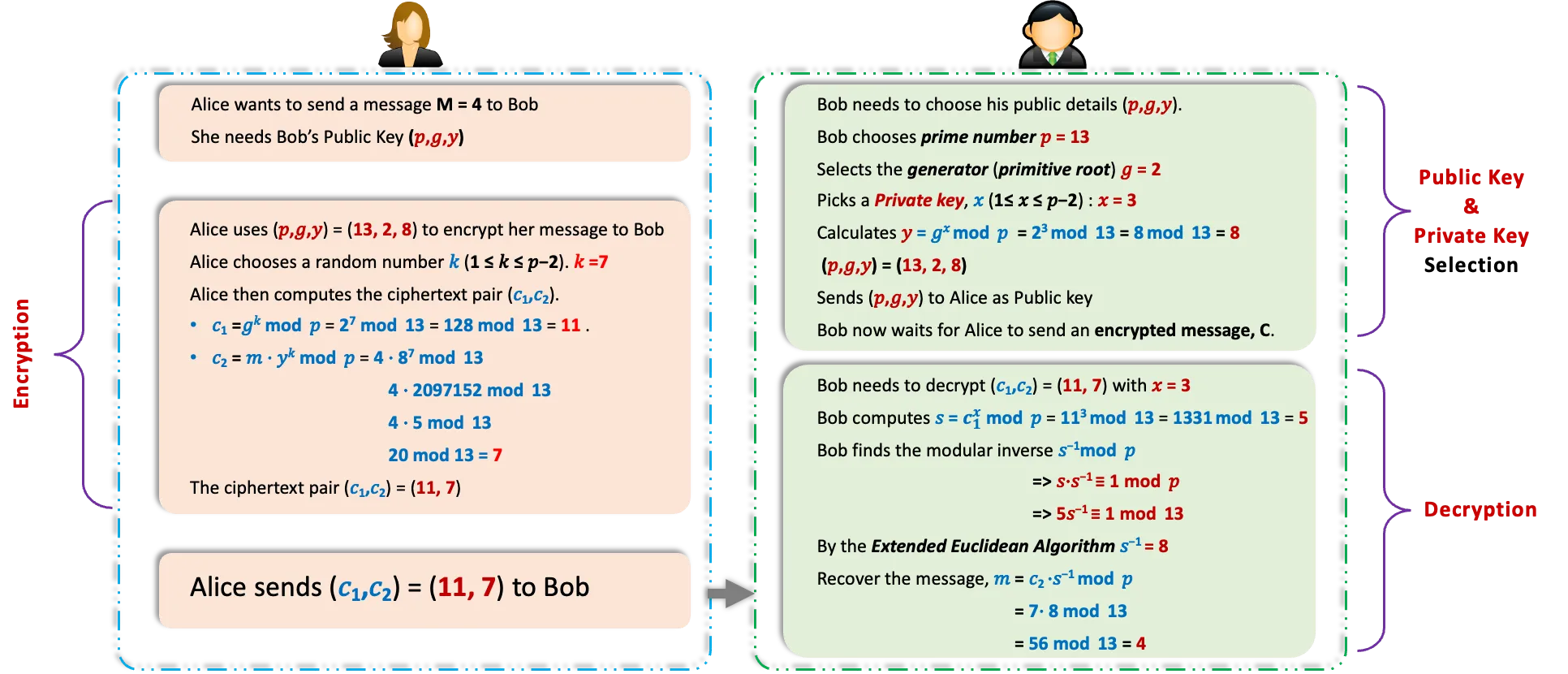
Key Generation
- Choose a large prime number, .
- Select a generator (): Pick a number (where ) that is a generator/primitive root modulo . This ensures can generate all numbers from to when raised to different powers.
- Pick a private key, : Choose a random integer 𝑥 (where ) as the private key.
- Compute the public key : Calculate . The public key is the triplet (), while remains secret.
Encryption
To encrypt a message (where ):
- Obtain the recipient’s public key: Use their ()
- Choose a random number : Select a random integer (where ). This is the session key and should be unique for each encryption.
- Compute the ciphertext pair:
- (this hides 𝑘 and is sent as part of the ciphertext).
- (this encrypts the message using the recipient’s public key).
- Send the ciphertext: The encrypted message is the pair ().
Decryption
To decrypt the ciphertext () using the private key :
- Compute the shared secret: Calculate . Since , this becomes .
- Find the modular inverse of : Compute (the number such that ).
- Recover the message: Calculate .
Why it works:
, so
.
ElGamal Example
ElGamal Encryption
Quiz
ElGamal Encryption Quiz -1
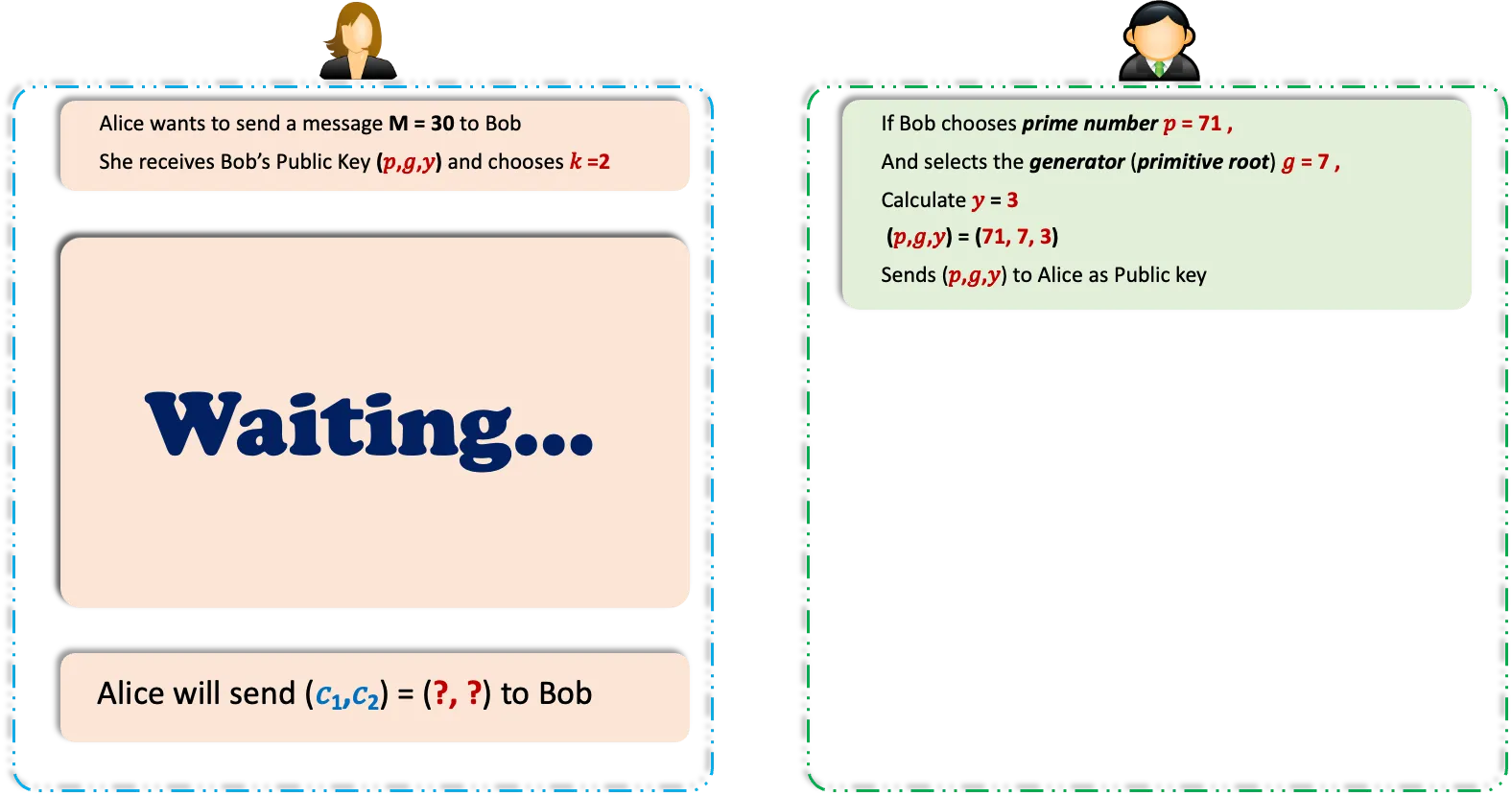
ElGamal Encryption Quiz - 2
Task:
Consider an ElGamal encryption scheme with a common prime and a primitive root (generator) . Given that the public key and User C chooses the random integer , what is the ciphertext for the message ?
Digital Signature
- A digital signature is a cryptographic technique used to prove the authenticity and integrity of a digital message or document.
- It is created using the sender’s private key and verified using the sender’s public key.
- It provides assurance that the message has not been modified in transit.
RSA Signature: Choosing Public and Private Keys
- Choose two prime numbers: and
- Compute
- Compute
- Choose e such that and . Let
- Find d such that
- Here, , so
(e, n) = (5, 51)
(d, n) = (13, 51)
for signing and verifying
RSA Signature: Signing and Verifying the Signature
- Let the message hash be h = 2
- Use the private key (d, n) = (13, 51)
- Compute signature: s = hd mod n
= 8192 mod 51
= 32
- Receiver uses the public key (e, n) = (5, 51)
-
Verify signature s = 32 by computing
h' = se mod n - If h' equals the original hash h = 2, the signature is valid
= 33554432 mod 51
= 2
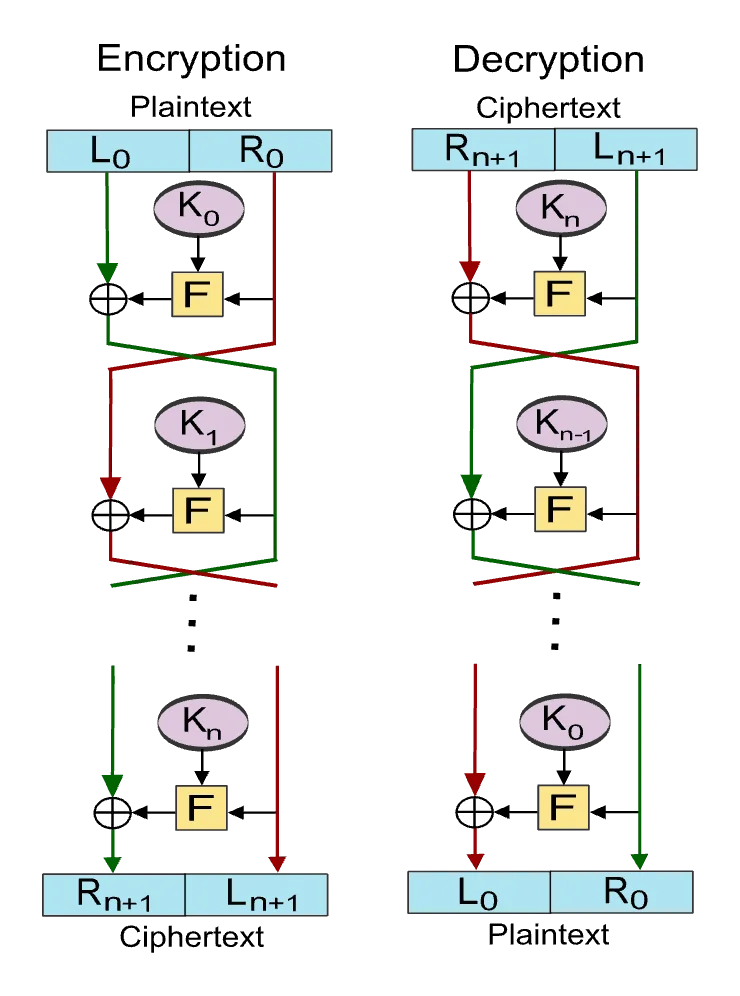
Feistel Cipher
- The Feistel Cipher is a symmetric encryption algorithm that uses a structure that divides the data into two halves and processes them through multiple rounds of permutation and substitution and then recombines them to produce the ciphertext.
- Its decryption process is essentially the same as encryption, just with the key schedule reversed.
How it works
- Splitting the Input: The plaintext block (say, 64 bits) is divided into two equal halves: a left half (L) and a right half (R). Eg. if the block is 64 bits, L₀ and R₀ = 32 bits each.
- Round Function:
- The right half (R) is fed into a round function F, which takes R and a round-specific subkey (derived from the main encryption key) as inputs. This function involve substitution boxes, or S-boxes, and permutations that scrambles the data.
- The output of F is XORed (exclusive OR) with the left half (L).
- The halves swap places: the old R becomes the new L, and the XOR result becomes the new R.
- Multiple Rounds: This process repeats for a set number of rounds (usally 16). Each round uses a different subkey, generated from the main key via a key schedule algorithm.
- Final Step: After the last round, the halves are concatenated to form the ciphertext.
Example
2 ROUNDS
- Plaintext: 16-bit plaintext
1010 1100 0110 0011 - Subkeys: Two 8-bit
- Round 1 subkey ():
1100 1010 - Round 2 subkey ():
0011 0101
- Round 1 subkey ():
- Round Function (F):
Define F(R, K) as R XOR K followed by a left circular shift of 2 bits.
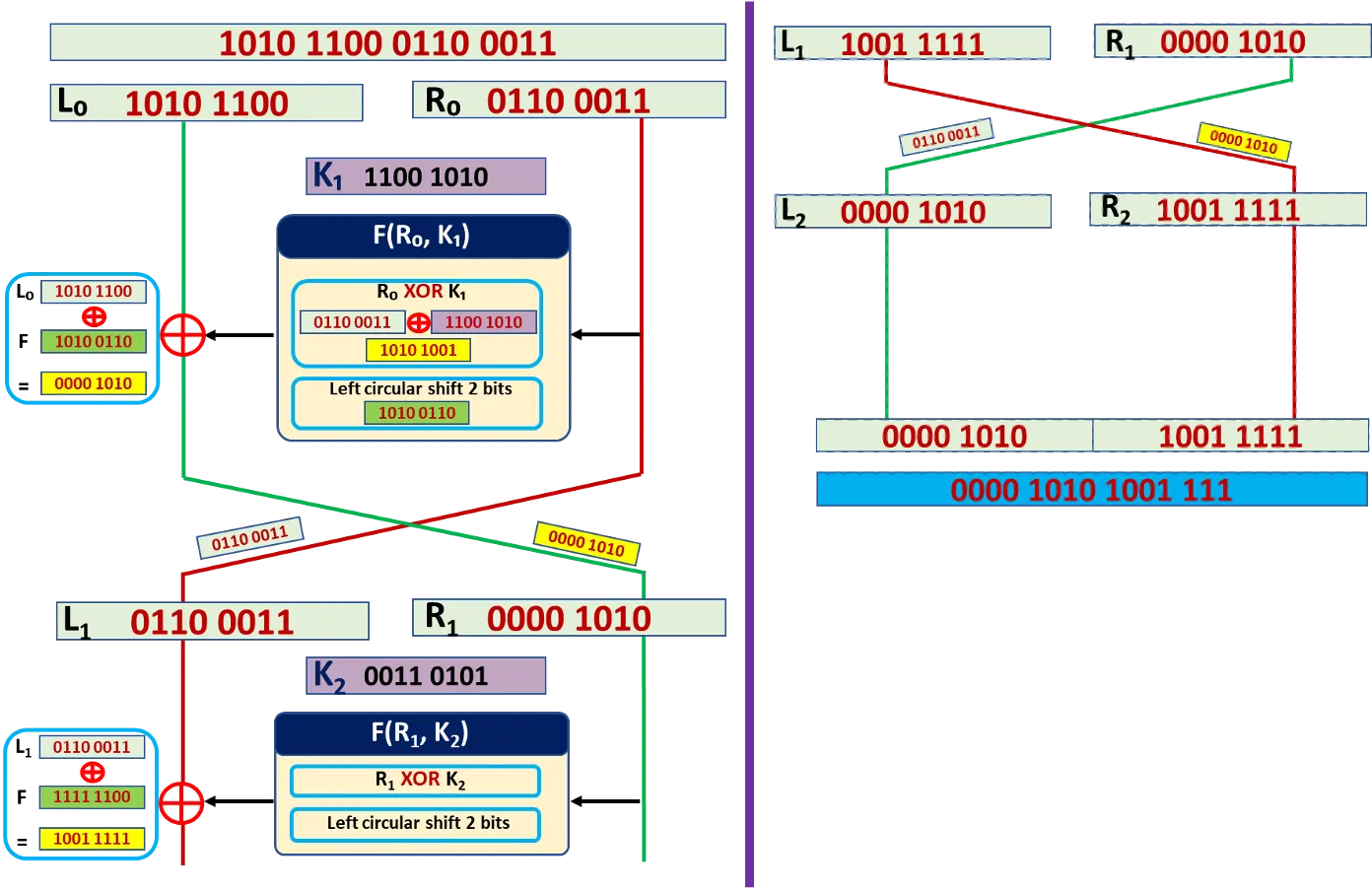
How it works
Round 1
- Apply to :
- (decimal 169)
- Left shift 2 bits: → (decimal 166)
- So,
- XOR with :
- (decimal 10)
- Swap:
- New
- New
After Round 1:
Round 2
-
Apply to :
- (decimal 63)
- Left shift 2 bits: → (decimal 252)
- So,
-
XOR with :
- (decimal 159)
-
Swap:
- New
- New
After Round 2:
Output
- Ciphertext: Concatenate and :
- (16 bits, decimal 175)
支持与分享
如果这篇文章对你有帮助,欢迎分享给更多人或赞助支持!
