Foundations of Security Week7 Seminar: Password Cracking & Secure Hashing

Learning Outcomes
Understand Hashing
Learn what hashing is and why it matters in security
Hashing vs Encryption
Understand the key difference between these two concepts
Generate & Compare Hashes
Practice creating password hashes using Python scripts
Dictionary Attack
Simulate a basic attack to crack weak password hashes
Rainbow Tables
Know what rainbow tables are and how attackers use them
Salting
Learn why salting protects passwords from attacks
What is Hashing
One-Way Function
Hashing converts any input (like a password) into a fixed-length string of characters. It's a mathematical one-way street.
Irreversible
Once hashed, you cannot retrieve the original input from the hash. This is what makes hashing perfect for password storage.
Avalanche Effect
Even a tiny change in input creates a completely different hash. This ensures uniqueness and security.
How Hashing Works
Input
Any Length
Hash Function
Processing
Output
Fixed Length
Real Example: Avalanche Effect
Input: password
5f4dcc3b5aa765d61d8327deb882cf99
Input: Password (capital P)
dc647eb65e6711e155375218212b3964
How Hashing Works
INPUT
(Any Length)
HASH
FUNCTION
OUTPUT
(Fixed 64 chars)
How Passwords Are Stored
User creates
password
System hashes
the password
Hash is stored
in database
Original password
is NEVER saved
Example — What a database actually stores:
| Username: | alice |
| Password Hash: | 5e884898da28047151d0e56f8dc6292773603d0d6... |
DANGEROUS: Plain Text
Database stores:
Username: john_doe
Password: mysecret123
- If database is breached, attacker sees all passwords immediately
- Users often reuse passwords across sites
- Legal and compliance violations (GDPR, etc.)
SECURE: Hashed Storage
Database stores:
Username: john_doe
Password Hash: 5f4dcc3b5aa765d61d8327deb882cf99
- Even if database is breached, passwords remain protected
- Attacker cannot reverse the hash to get original password
- Meets security compliance requirements
Common Hash Algorithms
MD5
AVOIDMessage Digest 5
Why Avoid:
Vulnerable to collision attacks. Can generate same hash for different inputs.
SHA-1
DEPRECATEDSecure Hash Algorithm 1
Why Deprecated:
Theoretical attacks proven. Google demonstrated real collision in 2017.
SHA-256
RECOMMENDEDSecure Hash Algorithm 256
Why Recommended:
Part of SHA-2 family. Currently secure with no practical attacks.
Hashing vs Encryption
Hashing
- One-Way Process
- No Key Required
- Fixed Output Length
Used For:
Password storage, data integrity verification, digital signatures
Encryption
- Two-Way Process
- Requires a Key
- Variable Output Length
Used For:
Data transmission, file protection, secure messaging
Dictionary Attack
What is a Dictionary Attack?
A dictionary attack uses a pre-compiled list of common passwords ("dictionary") and tries each one against a stolen hash.
Instead of trying every possible combination (brute force), attackers focus on passwords people actually use.
Common Password Lists Include:
Why It Works
People Use Weak Passwords
Studies show 23 million accounts use "123456"
Fast Processing
Modern GPUs can test billions of passwords per second
Password Reuse
59% of people reuse passwords across sites
Rainbow Tables
Understanding Rainbow Tables
A rainbow table is a pre-computed database of password hashes.
Attackers create these tables in advance, then use them to crack passwords instantly without computing hashes during the attack.
What a Rainbow Table Looks Like:
| Plain Text | MD5 Hash |
|---|---|
| password | 5f4dcc3b5aa765d61d... |
| 123456 | e10adc3949ba59abbe... |
| qwerty | d8578edf8458ce06fbc... |
| admin | 21232f297a57a5a7438... |
| letmein | 0d107d09f5bbe40cade... |
Why They're Dangerous
Instant Cracking
No computation needed during attack - just a table lookup
Mass Cracking
One table can crack millions of passwords
Freely Available
Tables for common passwords can be downloaded online
Comparison
| Attack Type | Main Idea | How it Works | Speed | Main Weakness | Best Defense |
|---|---|---|---|---|---|
| Dictionary Attack |
Tries likely passwords |
Uses a list of common words, names, and weak password patterns |
Faster than brute force |
Fails if password is uncommon and strong |
Strong, unique passwords and account lockout |
| Brute Force Attack |
Tries every possible combination |
Tests all possible characters and lengths until the correct password is found |
Slowest | Very time consuming for long complex passwords |
Long, complex passwords and rate limiting |
| Rainbow Table Attack |
Looks up precomputed hash values |
Compares stolen password hashes against a prebuilt table of password-hash pairs |
Very fast once table exists |
Fails against salted hashes |
Salting and strong hash algorithms |
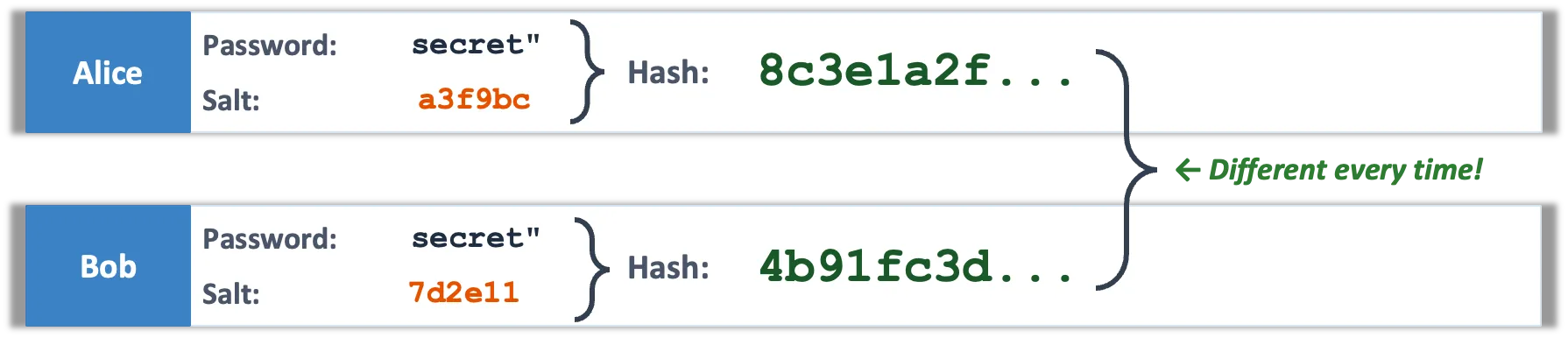
Salting
Understanding Salting
Salting is the process of adding a unique, random string to each password before hashing. This ensures that even identical passwords produce completely different hashes.
How Salting Works:
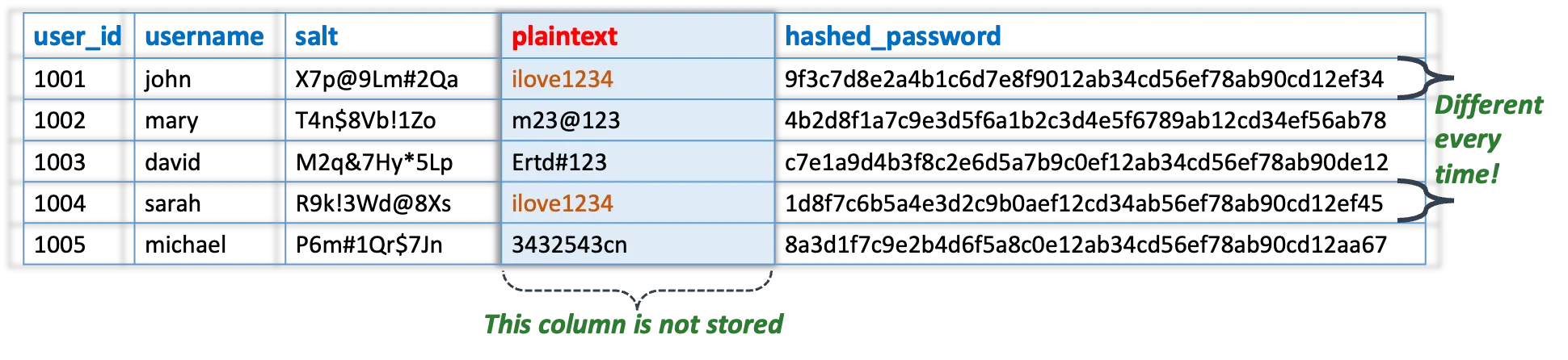
Storage Format
Database stores:
Salt is stored in plain text! Its purpose is to make pre-computed attacks impossible, not to be secret.
Simple Database illustration
| user_id | username | salt | hashed_password |
|---|---|---|---|
| 1001 | john | X7p@9Lm#2Qa | 9f3c7d8e2a4b1c6d7e8f9012ab34cd56ef78ab90cd12ef34 |
| 1002 | mary | T4n$8Vb!1Zo | 4b2d8f1a7c9e3d5f6a1b2c3d4e5f6789ab12cd34ef56ab78 |
| 1003 | david | M2q&7Hy*5Lp | c7e1a9d4b3f8c2e6d5a7b9c0ef12ab34cd56ef78ab90de12 |
| 1004 | sarah | R9k!3Wd@8Xs | 1d8f7c6b5a4e3d2c9b0aef12cd34ab56ef78ab90cd12ef45 |
| 1005 | michael | P6m#1Qr$7Jn | 8a3d1f7c9e2b4d6f5a8c0e12ab34cd56ef78ab90cd12aa67 |
Password Security Best Practices
1. Use Strong Hash Algorithms
Choose algorithms specifically designed for password hashing:
3. Enforce Strong Password Policies
Help users create secure passwords:
- Minimum 12 characters
- Require mixed case, numbers, symbols
- Check against known breached passwords
- Encourage password managers
2. Always Add Unique Salts
Every password must have its own random salt:
- Generate 16+ byte random salt per user
- Use cryptographically secure random generator
- Store salt alongside hash (not a secret)
4. Implement Additional Layers
Defense in depth approach:
- Rate limiting (prevent brute force)
- Account lockout after failed attempts
- Two-factor authentication (2FA)
- Pepper (optional secret salt)
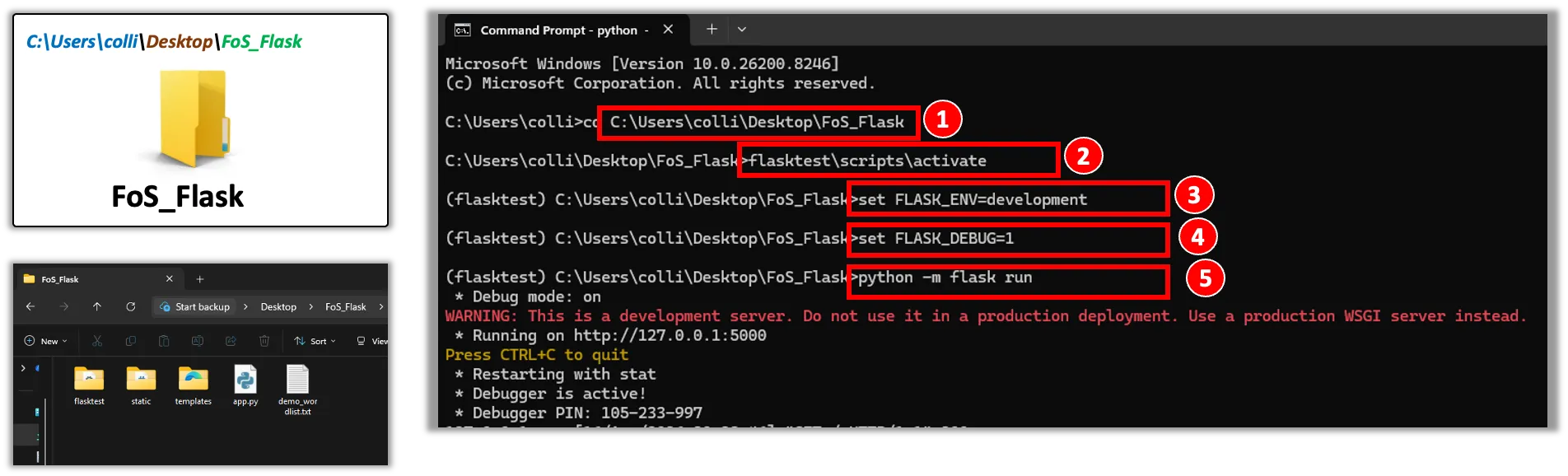
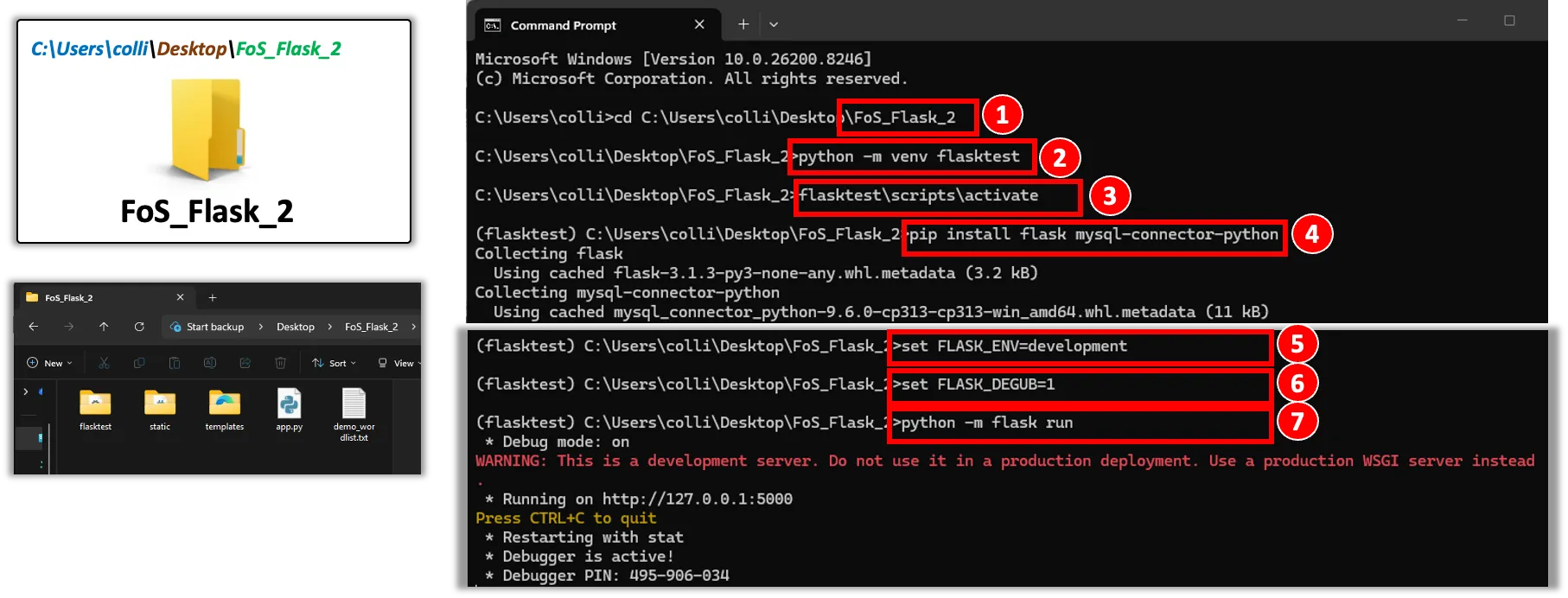
Password Hashing & Cracking Activity
Create a directory to work in, copy the extracted files and change to it by entering cd followed by that directory name.
Option 1: Use an old project’s already installed flask and virtual environment
Option 2: Create new virtual environment and install flask mysql-connector-python
支持与分享
如果这篇文章对你有帮助,欢迎分享给更多人或赞助支持!
