Foundations of Security Week8 Seminar: Digital Signature

Digital Signature
What is a digital signature
A digital signature is a cryptographic result attached to data that helps a receiver verify three things:
| 1 | 2 | 3 |
|---|---|---|
| Who sent it | It was not changed | Sender cannot easily deny it |
| Origin authentication | Integrity | Non-repudiation |
Important: a digital signature does not hide the message. Confidentiality comes from encryption, not from the signature itself.
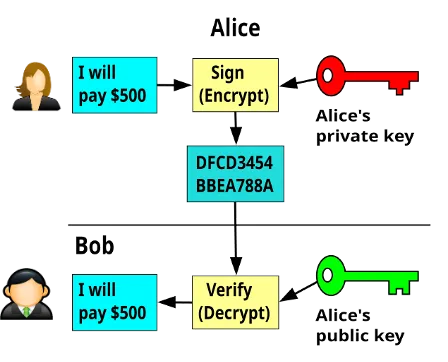
Simple idea: sign with the private key, verify with the public key.
Why we need it
Without protection, a digital file can be copied, edited, or impersonated in transit. The receiver needs proof of source and integrity.
If there is no digital signature
- Anyone can claim “I sent this.”
- A message can be modified silently.
- The receiver has no easy proof for a third party.
With a valid digital signature
- The public key checks the sender’s signature.
- Any change to the signed data breaks verification.
- It supports accountability in software, email, and documents.
Building blocks
| # | K | V | ID |
|---|---|---|---|
| Hash function | Private key | Public key | Certificate / PKI |
| Turns any message into a fixed-size digest. Small changes in the message create a very different digest. | Kept secret by the signer. It is used to create the signature. | Shared with others. It is used to verify a signature. | Binds a public key to an identity so that people know whose key they are using. |
How digital signatures work
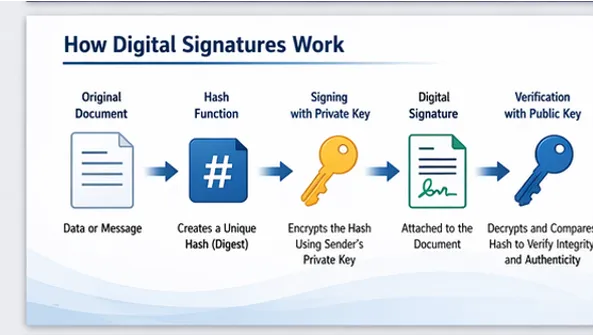
- Hash the message
A hash function converts the message into a short fingerprint. - Sign the hash
The sender uses a private key to sign that fingerprint. - Verify
The receiver recomputes the hash and uses the public key of the sender to check the signature.
Key insight
The signature is created over a hash, not by encrypting the whole document. That makes signing efficient even for large files.
Verification fails if
- the content changes
- the wrong public key is used
- the signature was forged
1. Hash
message
2. Encrypt hash
with private
key
3. Send
message
+ signature
4. Decrypt with
public key
5. Compute
message hash
& compare
hashes
Algorithms and common uses
Common signature algorithms
Widely taught and widely
deployed
Strong security with smaller
key sizes
Modern design; included in
FIPS 186-5 as Ed25519 /
Ed448 family
Common uses
Software signing
Proves a program or update
came from its publisher.
Signed email
Lets recipients verify sender
identity and tamper detection.
PDF / contract approval
Supports trusted document
workflows and audit trails.
Certificates on the web
Certificates themselves are
digitally signed by a CA.
Limitations and best practices
Limitations / risks
- If the private key is stolen, an attacker can create valid signatures.
- Verification only works if the receiver trusts the correct public key or certificate.
- A signature proves integrity and origin, but it does not prove the content is true or safe.
Best practices
- Protect private keys with strong storage and access control.
- Use trusted certificates and check validity / revocation status when relevant.
- Choose modern approved algorithms and key sizes.
RSA Signature: Choosing Public and Private Keys
- Choose two prime numbers: and
- Compute
- Compute
- Choose e such that and . Let
- Find d such that
- Here, , so
Public key
(e, n) = (3, 33)
Private key
(d, n) = (7, 33)
These keys are used for signing and verifying
RSA Signature: Signing the Message
- Let the message hash be
- Use the private
- Compute signature:
Therefore, the digital signature is
Sender uses private key to sign
RSA Signature: Verifying the Signature
- Receiver uses the public
- Verify signature by computing
- If equals the original hash , the signature is valid
Since , the signature is valid
Signature is
VALID
because
h' = h
2 = 2
Digital Signature (Activity)
Digital Signature Activity
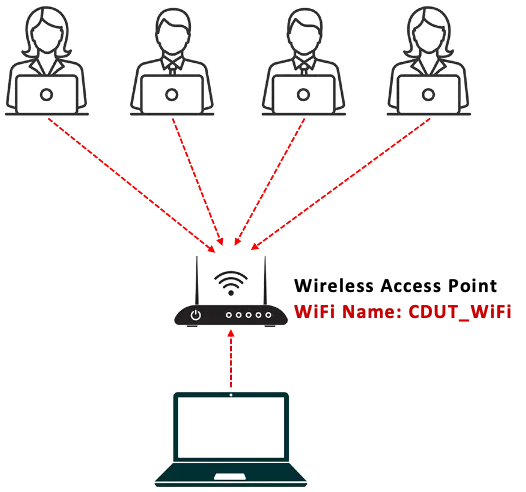
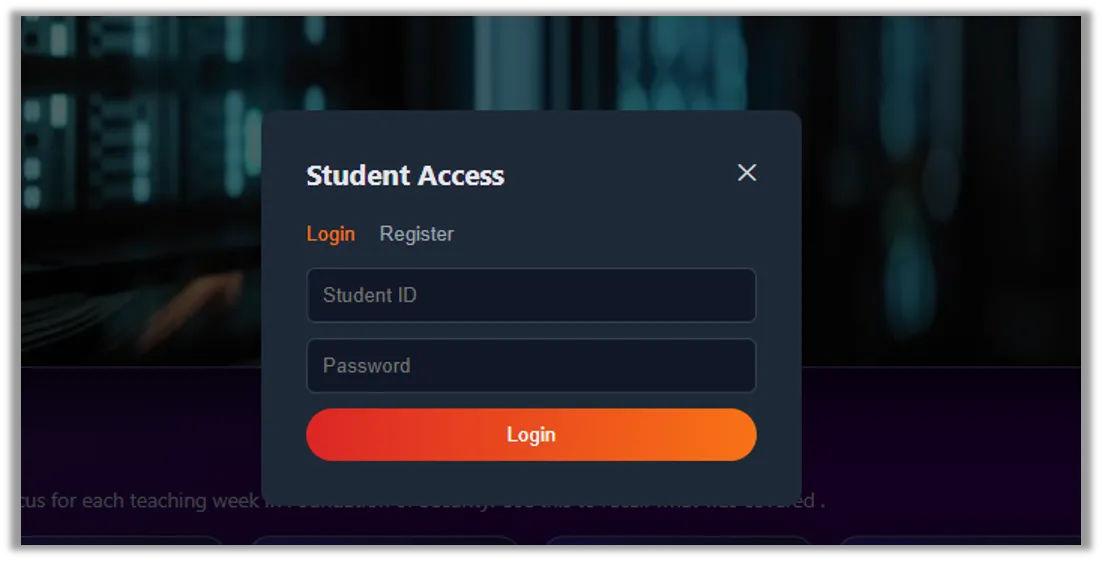
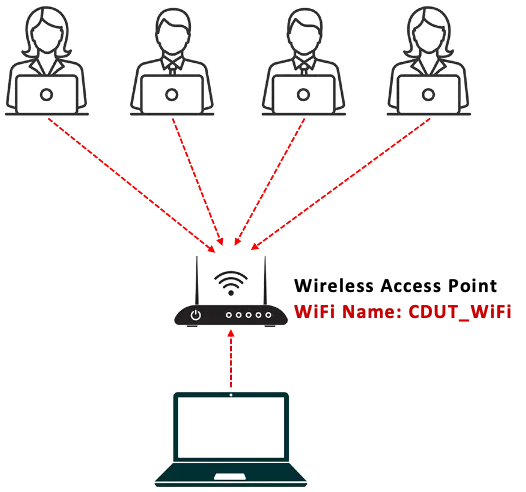
Connect to CDUT_WIFI, open your browser and Enter the URL http://172.20.X.X Click on the login button and register with your Student ID and appropriate Password. Login after successful registration
 |  |
|---|
Click on “Digital Signature” on the navigation tabs. Generate your key pairs (public key and private key)
Enter any message and click on “Sign and Store Message”
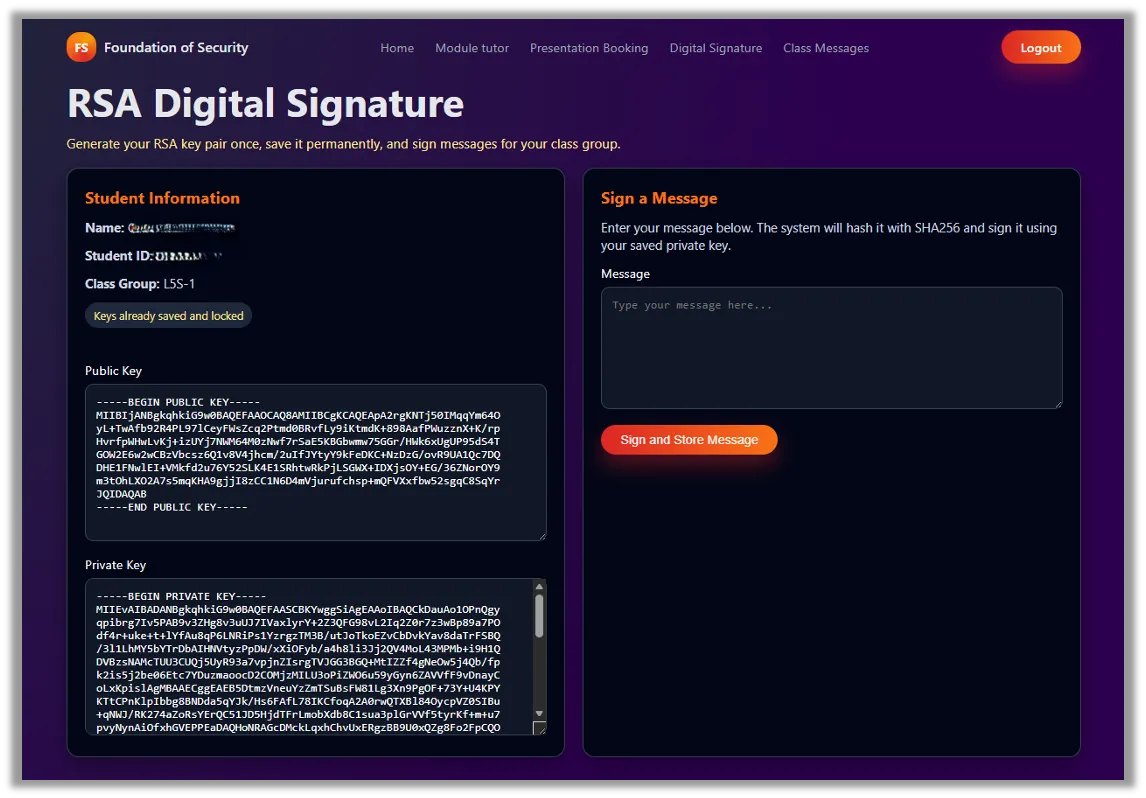
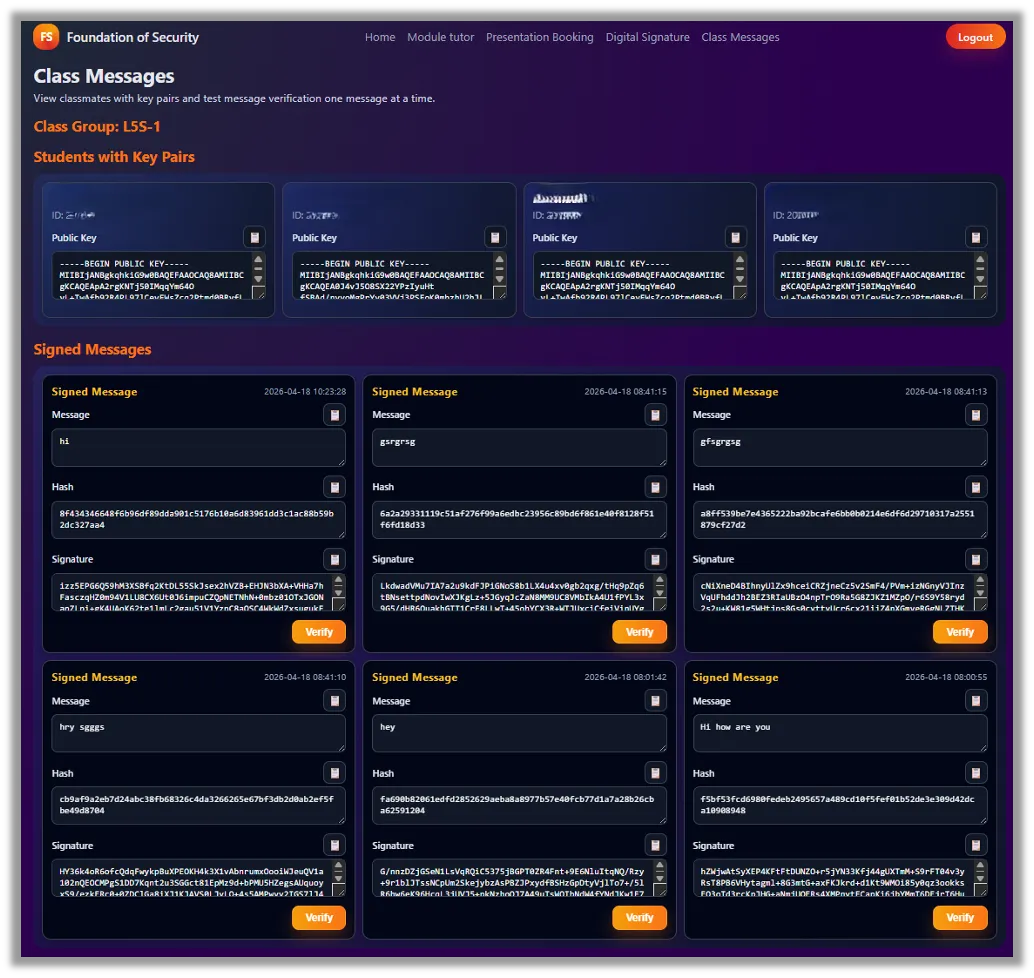
Click on “Class Messages” on the navigation tabs.
Verify the messages submitted by your friends on the page using their public key
Presentation Slot Booking
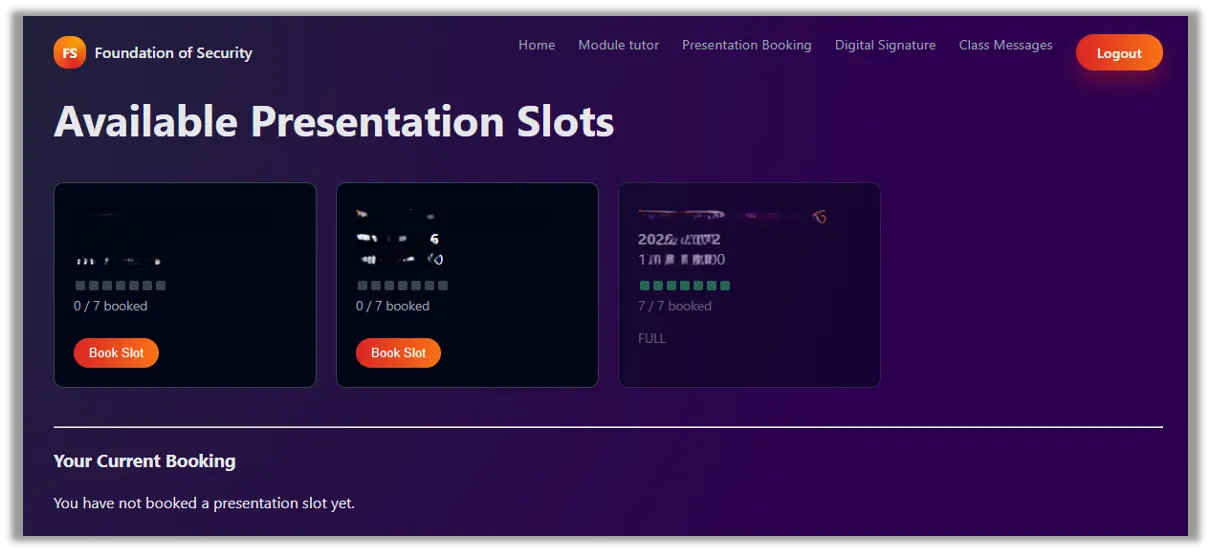
Connect to CDUT_WIFI, open your browser and Enter the URL http://172.20.X.X Click on the “Presentation Booking” tab to book an available slot for your class.
 |  |
|---|
支持与分享
如果这篇文章对你有帮助,欢迎分享给更多人或赞助支持!
