Foundations of Security Week3 Seminar: SQL Injection (1)

SQL Injection (1)
Objective
To introduce you to SQL injection attack, identify and demonstrate common SQL injection attacks, understand the underlying mechanisms that allow these attacks to succeed, and apply best practices in software development to prevent SQL injection vulnerabilities in web applications.

Exploiting Databases Through Code Insertion
What is it
A type of attack where an attacker exploits vulnerabilities in a web application’s input fields to execute malicious SQL commands. These commands allow attackers to interact with a database in unauthorized ways, often leading to data breaches or system compromise.
How does it happen
Attackers enter malicious SQL code into input fields (e.g., login forms, search boxes).
The application processes this input without proper validation.
Example
Bypassing Authentication (login page)
Extracting Data.
Setup
Tautology Based Injection
Using logical operations that always return true to manipulate query logic.
SELECT * FROM users WHERE username='anything' OR '1'='1';This injection uses a tautology (‘1’=‘1’ is always true) to bypass authentication logic and can potentially retrieve user records.
System query
SELECT * FROM students WHERE email = 'useremail' AND password = 'password';Attacker’s input
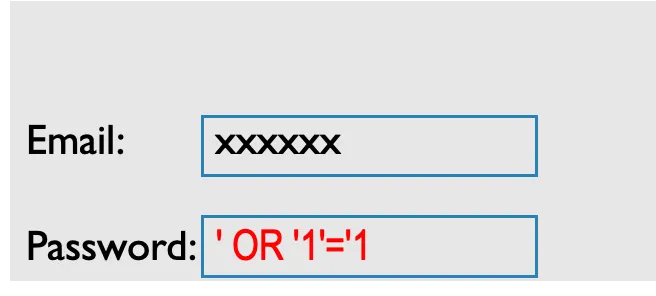
Resulting query
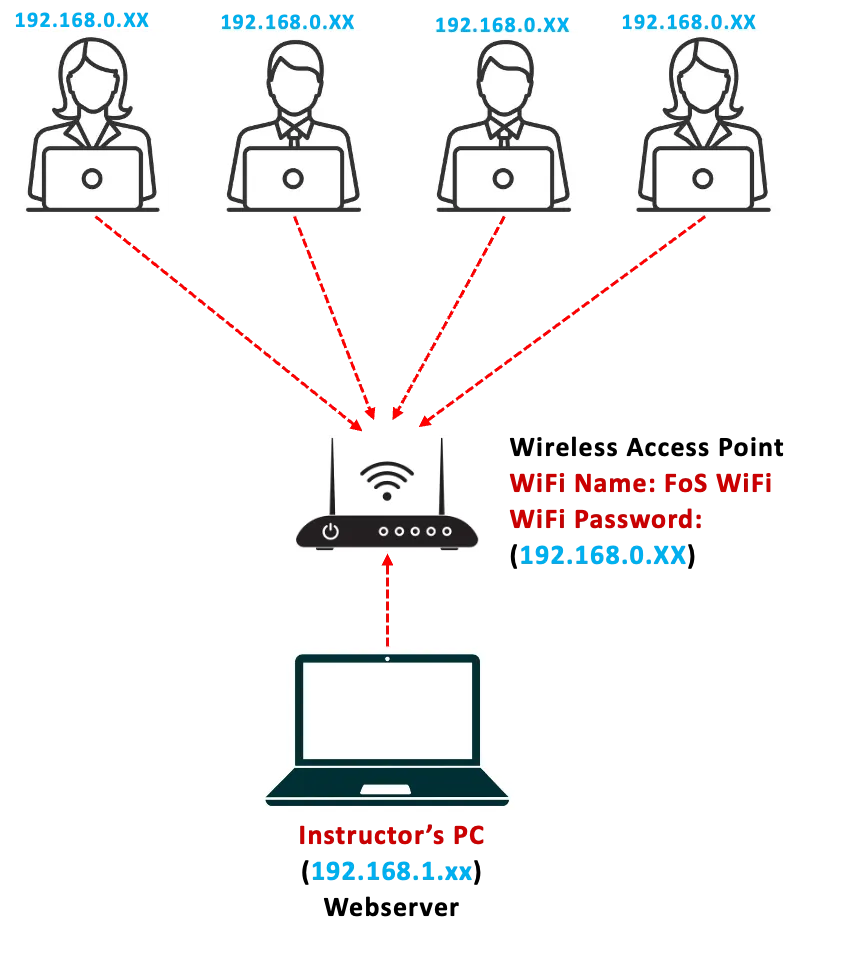
SELECT * FROM students WHERE email = 'xxxxxx' AND password = '' OR '1'='1';Task1: Connect to the Wireless Access Point/Router
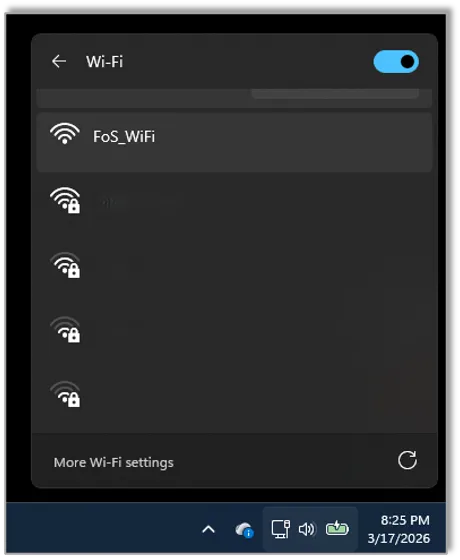
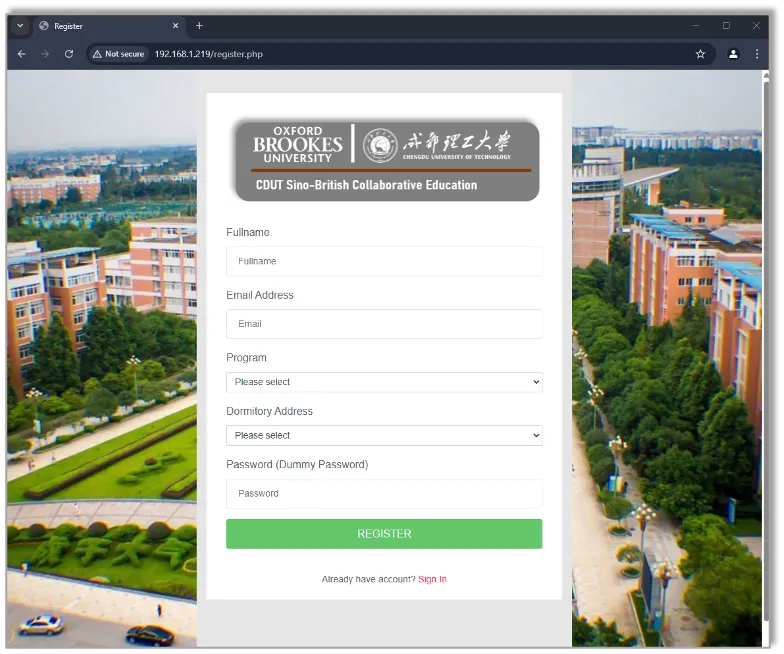
- Connect to the Wireless Access Point / Router as provided by the instructor (WiFi Name & Password will be provided)
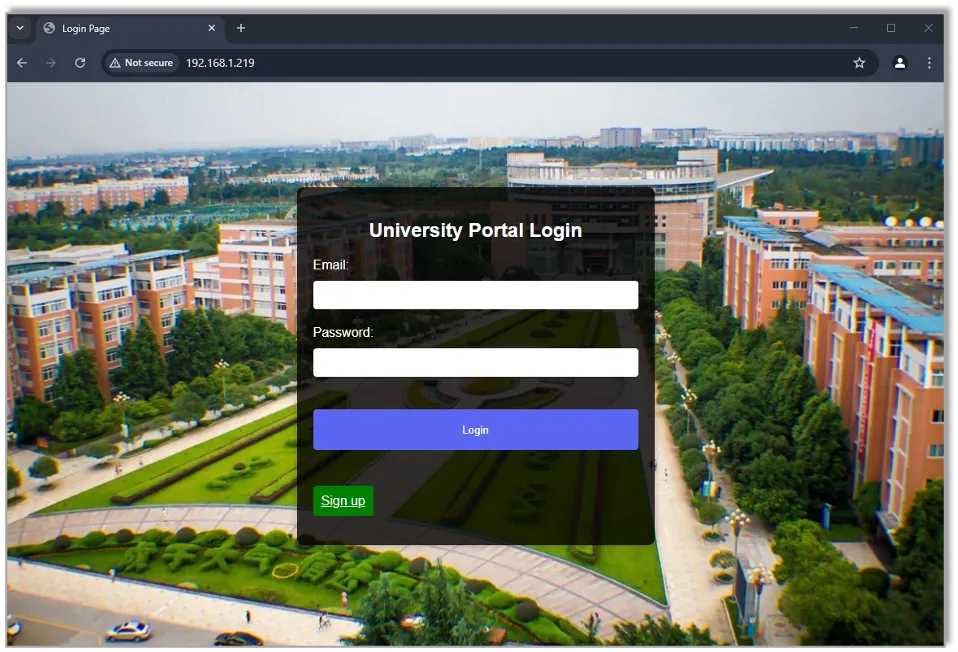
- Open you browser and enter the IP address (will be provided by the instructor) of the Webserver PC in your browser and hit “Enter”
- Access the demo web application interface
| 1 | 2-3 |
|---|---|
 | 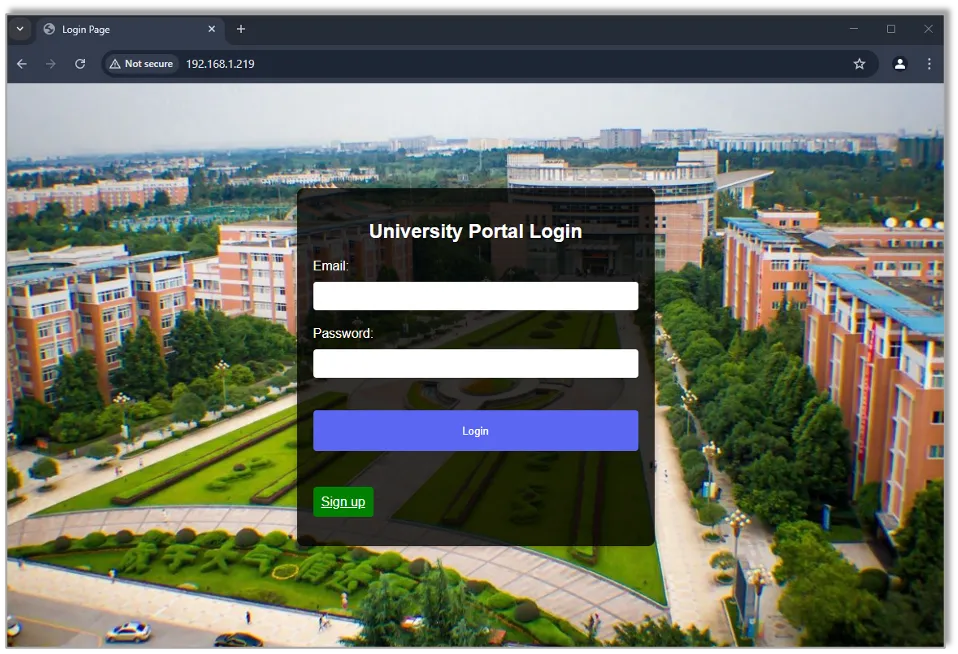 |
Task2: Sign up on the web application
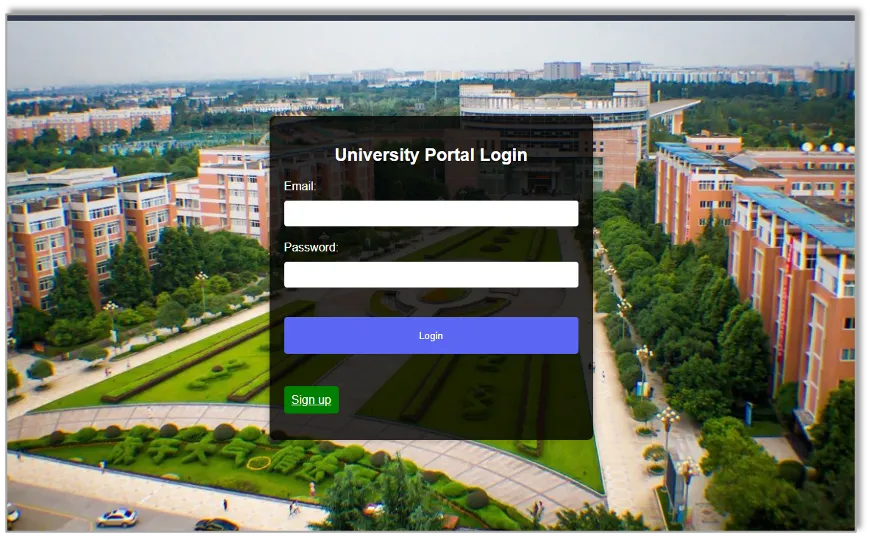
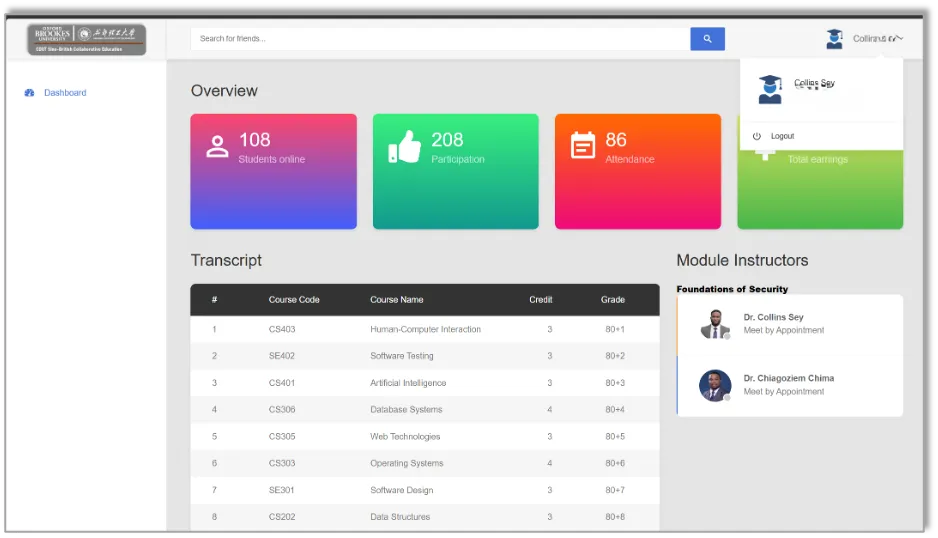
Task3: Login to the web application using your registered details. Logout after successful login
 |  |
|---|
Task4: Perform a Tautology Based SQL Injection to bypass the login authentication without your registered account
支持与分享
如果这篇文章对你有帮助,欢迎分享给更多人或赞助支持!
