Foundations of Security Week4 Seminar: SQL Injection (2)

SQL Injection (2)
Objective
To demonstrate and test the effectiveness of Tautology-Based SQL Injection in extracting data from a vulnerable database by manipulating SQL queries to always evaluate as true.
Setup
Tautology Based Injection
Using logical operations that always return true to manipulate query logic.
SELECT * FROM users WHERE username='anything' OR '1'='1';This injection uses a tautology ('1'='1' is always true) to bypass authentication logic and can potentially retrieve user records.
System query
SELECT * FROM students WHERE email = 'useremail' AND password = 'password';Attacker’s input
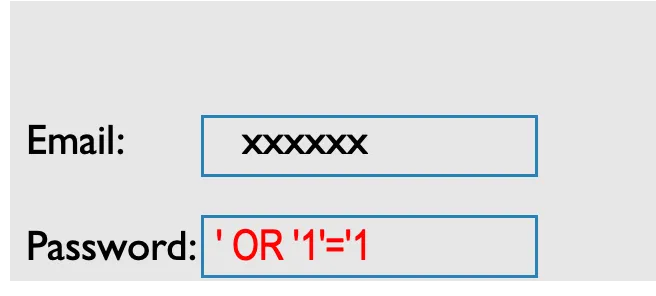
Resulting query
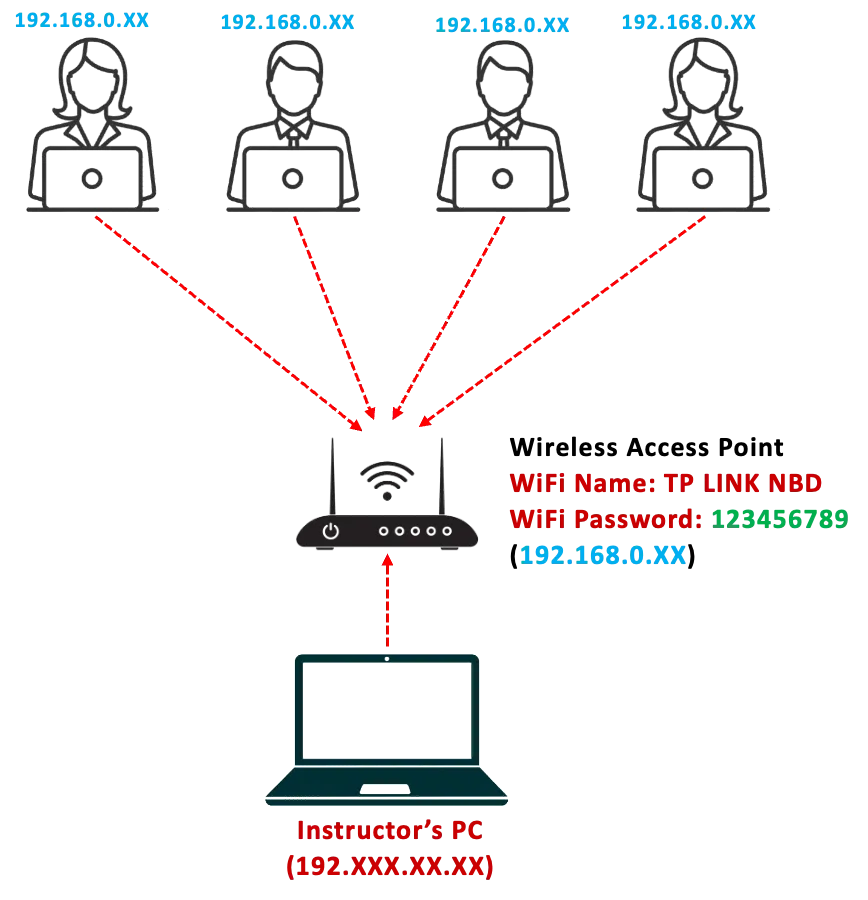
SELECT * FROM students WHERE email = 'xxxxxx' AND password = '' OR '1'='1';Task1: Connect to the Wireless Access Point/Router
- Connect to the Wireless Access Point/ Router as provided by the instructor (WiFi Name & Password will be provided)
- Open your browser and enter the IP address (will be provided by the instructor) of the Webserver PC in your browser and hit “Enter”
- Access the demo web application interface
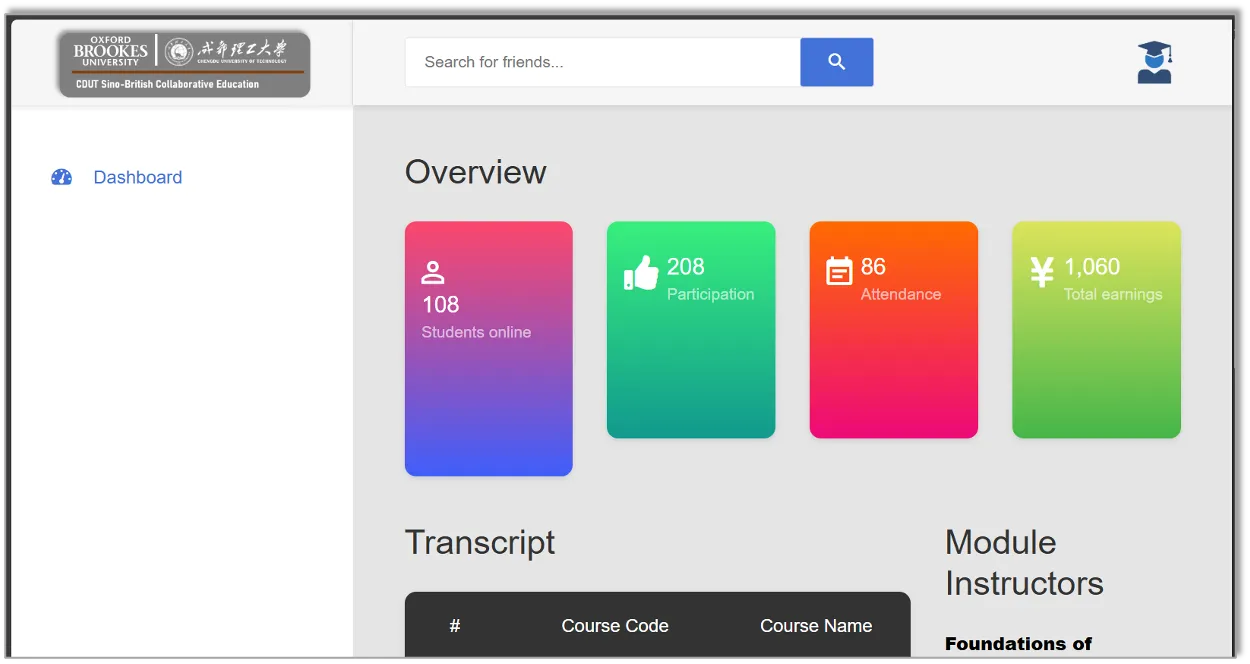
Task2: Perform a Tautology Based SQL Injection to Extract Data (Retrieve all registered students – friends) from the university portal
Avoiding Tautology Based SQL Injection
Use Prepared Statements and Parameterized Queries
This is one of the most effective defenses against SQL injection. By using prepared statements, the SQL code and the data are bound separately, ensuring that the data is treated only as data and not executable code. Both PDO (PHP Data Objects) and MySQLi in PHP support prepared statements.
Whitelist Input Validation
Validate and sanitize user inputs to ensure they conform to expected and allowed formats. For example, if a field expects a number, ensure the input is a number. This doesn’t prevent SQL injection by itself but is a good additional layer of defense.
Escape All User Inputs
If you’re not using prepared statements or stored procedures, escaping user inputs is a must to ensure that special characters in the input don’t lead to malicious SQL being executed.
Avoiding Tautology Based SQL Injection
dash_b
$sql_searchlist = "SELECT * FROM students WHERE Student_Name LIKE '%$std_name%'";// SQL injection prone$result_searchlist = $conn->query($sql_searchlist);if ($result_searchlist->num_rows > 0){dash_n
$sql_searchlist = "SELECT * FROM students WHERE Student_Name LIKE CONCAT('%', ?, '%')";// Prepare a parameterized SQL statement$sql_searchlist = $conn->prepare($sql_searchlist);
// Bind the user input to the prepared statement$sql_searchlist->bind_param("s", $std_name);
// Execute the prepared statement$sql_searchlist->execute();
// Retrieve the results$result_searchlist = $sql_searchlist->get_result();if ($result_searchlist->num_rows > 0){支持与分享
如果这篇文章对你有帮助,欢迎分享给更多人或赞助支持!
