Lecture Outline#
- Review of RSA cryptographic algorithm
- Public key and Private key generation in RSA
- RSA encryption and decryption process
- Introduction to Chosen Ciphertext Attack (CCA) on RSA
- Understanding how attackers exploit decryption systems
Learning Outcomes#
By the end of this lecture, students should be able to:
- Explain the RSA key generation process
- Identify the steps for generating public and private keys
- Apply the Extended Euclidean Algorithm to compute the private key
- Perform RSA encryption and decryption
- Explain the concept of chosen ciphertext attacks on RSA
Key Generation#
| 1. Select Primes | 2. Compute n | 3. Calculate ϕ(n) | 4. Choose e | 5. Compute d |
|---|
| Choose two large prime numbers p and q. These must be kept secret. | Calculate the modulus n by multiplying p and q. This is part of both keys. | Compute Euler’s totient function using the formula (p−1)×(q−1). | Select public exponent e where 1<e<ϕ(n) and gcd(e,ϕ(n))=1. | Calculate private exponent d as the modular multiplicative inverse of e. |
| p,q=primes | n=p×q | ϕ(n)=(p−1)(q−1) | 1<e<ϕ(n)
gcd(e,ϕ(n))=1 | (d×e)≡1modϕ(n) |
| Public Key | Private Key |
|---|
(n, e)
Share freely with anyone | (n, d)
Keep secret at all times |
Public Key Generation#
Public Keys of Alice#
💬 Wants to send a message
Alice needs to encrypt her message
so only Bob can read it.
🔑 Needs a key pair
She must generate public and
private keys for encryption.
📤 Shares public key
Her public key can be shared with
anyone, including Bob.
↔️
Secure Channel
End-to-end encryption
📩 Wants to receive message
Bob needs to decrypt Alice's message
securely.
🔑 Needs a key pair
He must also generate public and
private keys.
🔒 Keeps private key secret
His private key must never be shared
with anyone.
Public Keys of Alice & Bob#
Both parties generate their public keys simultaneously
1
Select Prime Numbers
PA = 61,
QA = 53
2
Calculate modulus n
nA = PA × QA
= 61 × 53 = 3233
3
Choose Public Exponent e
eA must satisfy:
✓ 1 < eA < φ(nA)
✓ gcd(eA, φ(nA)) = 1
eA = 17
Calculate Euler's Totient Function
φ(n
A) = (P
A - 1) × (Q
A - 1)
= (61 - 1) × (53 - 1) = 60 × 52 =
3120
🔑
Alice's Public Key
(nA = 3233, eA = 17)
1
Select Prime Numbers
PB = 3,
QB = 11
2
Calculate modulus n
nB = PB × QB
= 3 × 11 = 33
3
Choose Public Exponent e
eB must satisfy:
✓ 1 < eB < φ(nB)
✓ gcd(eB, φ(nB)) = 1
eB = 7
Calculate Euler's Totient Function
φ(n
B) = (P
B - 1) × (Q
B - 1)
= (3 - 1) × (11 - 1) = 2 × 10 =
20
🔑
Bob's Public Key
(nB = 33, eB = 7)
Public Keys of Alice#
Mathematical constraints for selecting the public exponent e
✓
Greater than 1
✓
Less than φ(n) (Euler's totient)
Why:
Ensures e is in the valid multiplicative group
e must be co-prime with φ(n):
gcd(e, φ(n)) = 1
✓
No common factors with φ(n)
✓
Ensures multiplicative inverse exists
Why:
Required for the decryption key to exist
e × d ≡ 1 (mod φ(n))
Must have a multiplicative inverse d
✓
d is the private key
✓
Found using Extended Euclidean Algorithm
Why:
Enables encryption/decryption symmetry
Alice's φ(n)
φ(3233) = 3120
💡
Formula: φ(n) = (p-1) × (q-1)
Private Key of Alice#
👩
Alice
Private Key Calculation
Public Values
nA = 3233
eA = 17
Prime Factors
PA = 61
QA = 53
Calculate Euler's Totient Function
φ(nA) = (PA - 1) × (QA - 1)
= (61 - 1) × (53 - 1) = 60 × 52 = 3120
Step-by-Step Calculation
1
Set Up the Congruence Equation
Find dA such that:
eA × dA ≡ 1 (mod φ(nA))
17 × dA ≡ 1 (mod 3120)
2
Apply Extended Euclidean Algorithm
3120 = 17(183) + 9
17 = 9(1) + 8
9 = 8(1) + 1
8 = 1(8) + 0
Working backwards to find the inverse...
1 = 9 + 8(-1)
1 = 9 + [17 + 9(-1) ] (-1)
1 = 9 + 17 (-1) + 9(1)
1 = 17 (-1) + 9(2)
1 = 17 (-1) + [3120 + 17(-183)](2)
1 = 17 (-1) + [3120(2) + 17(-366)]
1 = 17 (-1) + 3120(2) + 17(-366)
1 = 17 (
-367) + 3120(2)
3120 + (-367) = 2753
3
Solution: Private Key
dA = 2753
Verification: 17 (2753) = 46801 mod 3120 = 3120(15) + 1 mod 3120 ✓
🔒
Alice's Private Key:
dₐ = 2753
(Keep Secret!)
🔑
Used for decrypting messages
Private Key of Bob#
👨
Bob
Private Key Calculation
Public Values
nB = 33
eB = 7
Prime Factors
PB = 3
QB = 11
Calculate Euler's Totient Function
φ(nB) = (PB - 1) × (QB - 1)
= (3 - 1) × (11 - 1) = 2 × 10 = 20
Step-by-Step Calculation
1
Set Up the Congruence Equation
Find dB such that:
eB × dB ≡ 1 (mod φ(nB))
7 × dB ≡ 1 (mod 20)
2
Apply Extended Euclidean Algorithm
20 = 7(2) + 6
7 = 6(1) + 1
6 = 1(6) + 0
Working backwards to find the inverse...
1 = 7 + 6(-1)
1 = 7 + [20 + 7(-2) ] (-1)
1 = 7 + [20(-1) + 7(2)]
1 = 7(3) + 20(-1)
3
Solution: Private Key
dB = 3
Verification: 7 (3) = 21 mod 20 = 1 mod 20 ✓
🔒
Bob's Private Key:
dB = 3
(Keep Secret!)
🔑
Used for decrypting messages
Key Pairs Summary#
🔓
Public Key
SHARE
Modulus n
3233
Exponent e
17
🔒
Private Key
SECRET
🔓
Public Key
SHARE
Modulus n
33
Exponent e
7
🔒
Private Key
SECRET
RSA Encryption & Decryption#
With their key pairs generated, Alice and Bob can now securely exchange encrypted messages. The foundation of RSA encryption is established.
✈️
Alice Encrypts
Using Bob's public key
↔️
Secure Transfer
Encrypted message sent
🔒
Bob Decrypts
Using his private key
Encryption & Decryption#
Encryption and Decryption Process#
The sender uses the recipient's public key (n, e) to encrypt
the plaintext message M into ciphertext C.
C
Ciphertext (encrypted message)
M
Plaintext message (as number)
n
Modulus (part of public key)
The recipient uses their private key (n, d) to decrypt the
ciphertext C back into the original plaintext message M.
M
Recovered plaintext message
C
Ciphertext (encrypted message)
d
Private exponent (secret)
n
Modulus (same as public key)
Only the holder of the private key d can decrypt the message. Even if an attacker knows the public key (n, e) and intercepts the ciphertext C, they cannot compute d without factoring n into p and q — a computationally infeasible task for large keys.
Encryption and Decryption Process#
👤Alice's Keys
Public Key:
nA = 3233, eA = 17
👤Bob's Keys
Public Key:
nB = 33, eB = 7
🔒Step 1: Encryption (Alice)
Alice uses Bob's public key to encrypt the message:
C = MeB mod nB
C = 27 mod 33
= 128 mod 33
= 29 mod 33
Ciphertext
C = 29
🔓Step 2: Decryption (Bob)
Bob uses his private key to decrypt:
M = CdB mod nB
M = 293 mod 33
= 24389 mod 33
= 2 mod 33
Recovered Message
M = 2
Quiz#
👤Alice's Keys
Public Key:
nA = 3233, eA = 17
👤Bob's Keys
Public Key:
nB = 33, eB = 7
🔒Step 1: Encryption (Alice)
Alice uses Bob's public key to encrypt the message:
C = MeB mod nB
C = 57 mod 33
= 78125 mod 33
= 14 mod 33
Ciphertext
C = 14
🔓Step 2: Decryption (Bob)
Bob uses his private key to decrypt:
M = CdB mod nB
M = 143 mod 33
= 2744 mod 33
= 5 mod 33
Recovered Message
M = 5
Chosen Ciphertext Attacks (CCA) on RSA Algorithm#
The Chosen Ciphertext Attack (CCA) on the RSA algorithm is a type of cryptographic attack where the attacker uses the decryption capabilities of a system/users to decrypt messages by choosing a series of ciphertexts and using the results to deduce the plaintext or the encryption key.
Chosen Ciphertext Attack on RSA#
Normal RSA Communication Flow
👩
Alice
Sender
Has Bob's Public Key:
(eB, nB)
→
Encryption
C = MeB mod nB
→
☁️ Public Channel (Encrypted)
👨
Bob
Receiver
Has Private Key:
(dB, nB)
Alice uses Bob's public key to encrypt
message M:
C = 27 mod 33 = 29
Ciphertext C travels through the public channel.
Even if intercepted, it's unreadable without the
private key.
Bob uses his private key to decrypt:
M = 293 mod 33 = 2
Public Keys of Alice#
Key Generation
PA = 61, QA = 53
nA = 3233
φ(nA) = 3120
eA = 17
dA = 2753
Has Access To
🔑
Own keys
🌍
Bob's public key
Capabilities
👁️
Intercepts all traffic
📝
Modifies messages
🔑
Knows public keys
Attack Parameters
Chooses:
r = 2
(coprime to nB = 33)
Goal
Recover M without dB
Key Generation
PB = 3, QB = 11
nB = 33
φ(nB) = 20
eB = 7
dB = 3
Has Access To
🔑
Own private key
🔓
Alice's public key
Receives
C' = 16
(not the original C)
Alice wants to send message M=2 to Bob. The attacker intercepts the communication and substitutes ciphertext C with manipulated C’
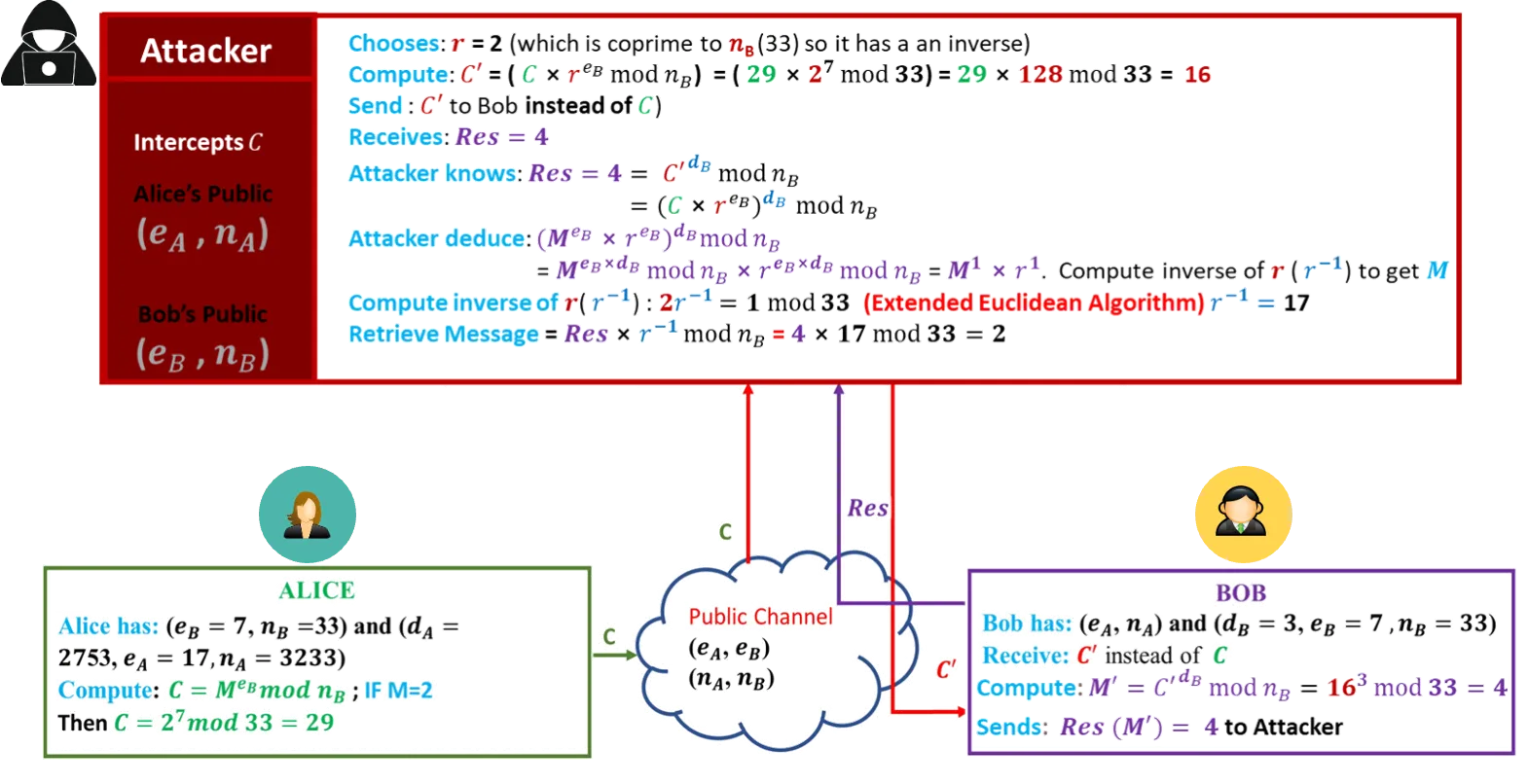
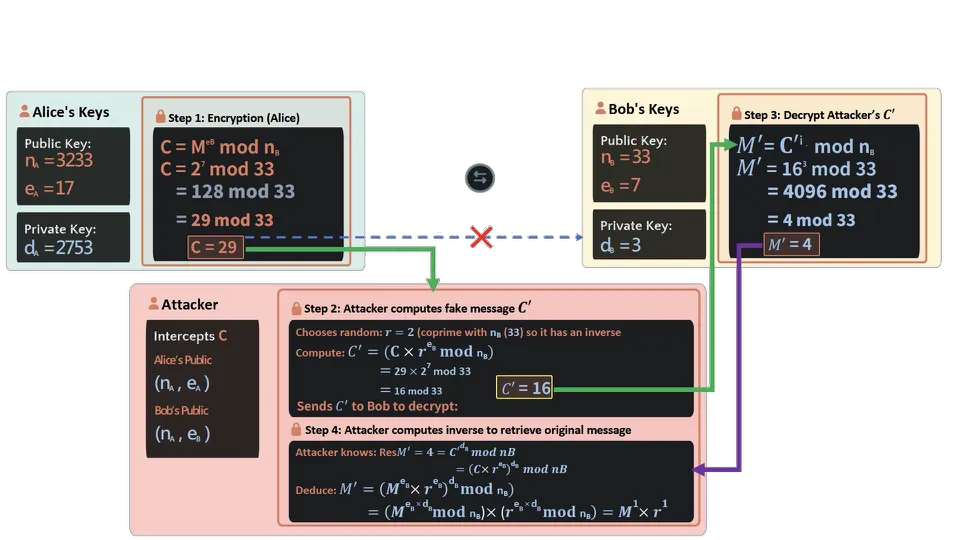
Chosen Ciphertext Attack on RSA#
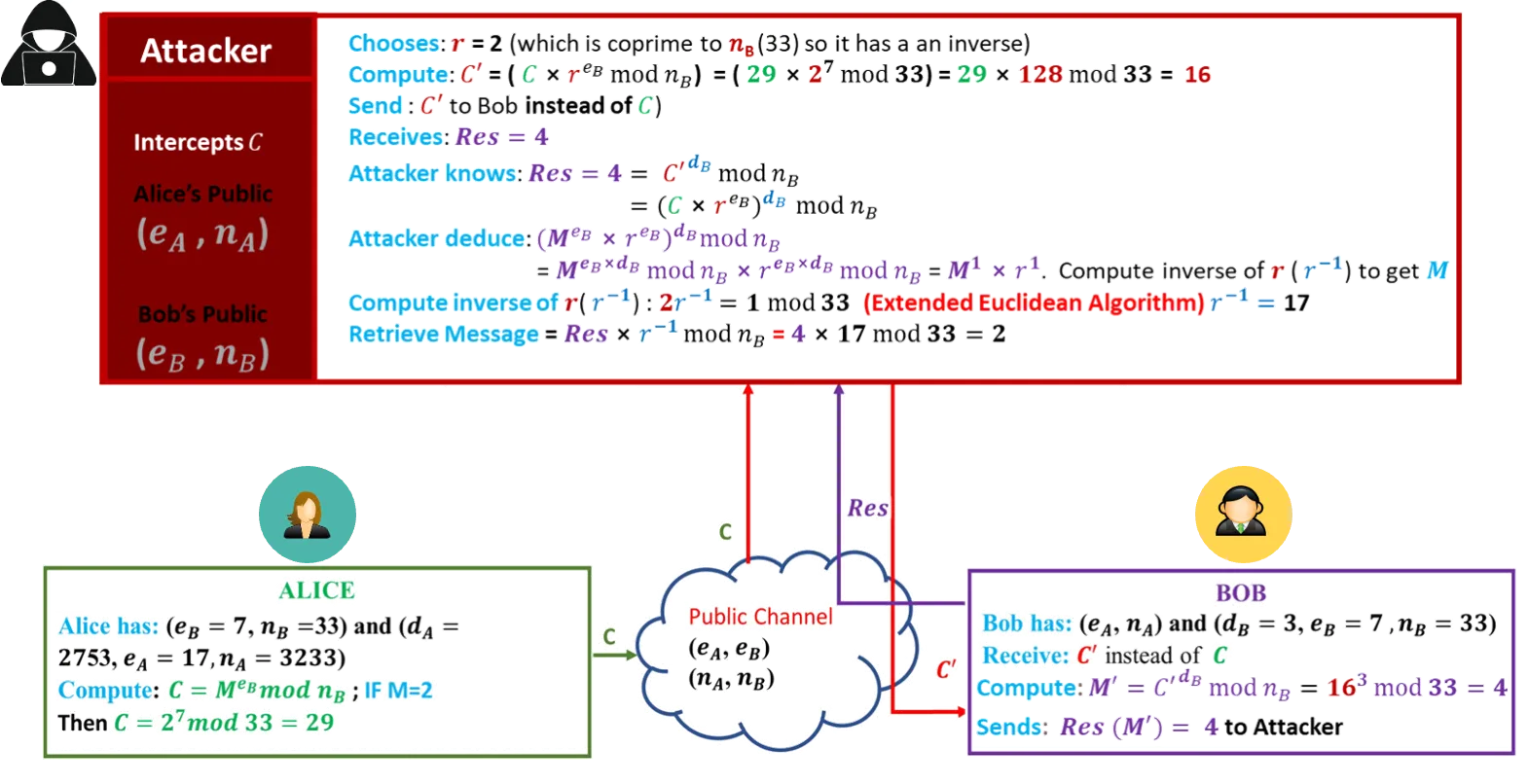
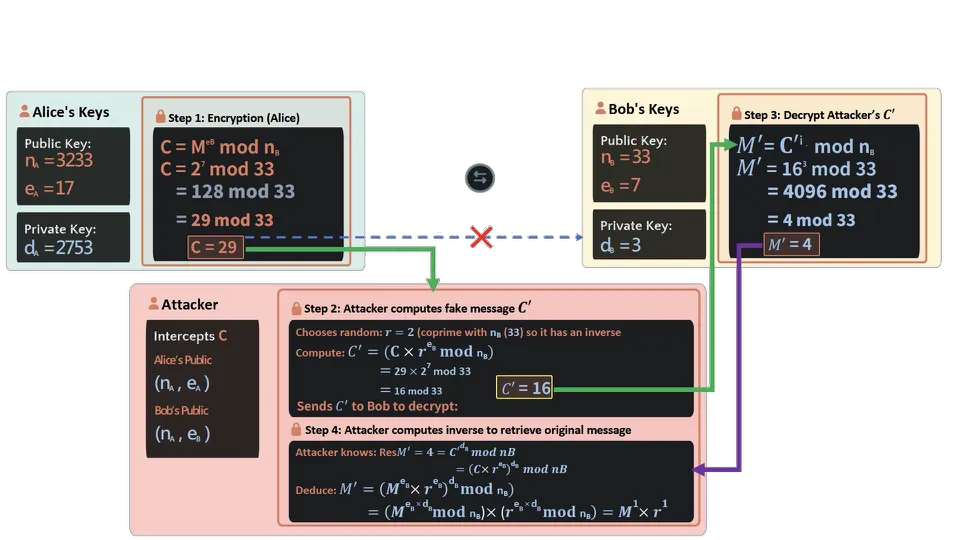
Attacker
Intercepts C
Alice's Public
(nA, eA)
Bob's Public
(nB, eB)
🔒 Step 2: Attacker computes fake message C'
Chooses random: r = 2 (coprime with nB(33) so it has an inverse)
Compute: C' = (C × reB mod nB)
= 29 × 27 mod 33
= 16 mod 33
Sends C' to Bob to decrypt:
C' = 16
🔒 Step 4: Attacker computes inverse to retrieve original message
Attacker knows: ResM' = 4 = C'dBmod nB
= (C×reB)dBmod nB
Deduce: M' = (MeB×reB)dBmod nB
= (MeB×dBmod nB)×(reB×dBmod nB) = M1×r1
Compute inverse of r to get M: M1 × r1 (r-1)
Inverse: 2 (r-1) ≡ 1 mod nB
= r-1 = 17
Retrieve M: Res × 17 mod nB
= 4 × 17 mod 33
= 68 mod 33
= 2
Alice encrypts M=2 using Bob's public key (eB=7, nB=33):
C = MeB mod nB
C = 27 mod 33 = 29
Attacker captures C=29 and chooses r=2 (coprime to 33):
C' = (C × reB) mod nB
C' = (29 × 27) mod 33
C' = (29 × 128) mod 33 = 16
Attacker forwards C' = 16 to Bob instead of the original C = 29
Bob decrypts using his private key (dB=3, nB=33):
Res = C'dB mod nB
Res = 163 mod 33 = 4
Bob sends Res=4 back (thinking it's related to the original message):
Res = 4
Attacker computes r-1 mod 33 = 17 using Extended Euclidean Algorithm:
M = Res × r-1 mod nB
M = 4 × 17 mod 33
M = 2 ✓
Assignment#
Assignment: Complete this exercise and submit during seminar class
Alice’s Public key: nA=3233 and eA=17
Alice’s Private key: dA=2753 | Bob’s Public key: nB=33 and eB=7
Bob’s Private key: dB=3 |
|---|
Task:
If Alice wants to send the message M=5 to Bob, perform the chosen ciphertext attack and retrieve the original message if the attacker chooses random number r=2. Show the following:
Modified Ciphertext (C′): _____________
Bob’s Response: _____________
Attacker’s Recover Process: _____________
Show how you computed your answers.
Only handwritten solutions.
No copy-paste will be accepted.
Security Strength & Key Sizes#
📏 NIST Recommendations for RSA Key Sizes
2048-bit RSA
Security: ~112 bits | Status: Acceptable until 2030
Current Standard
3072-bit RSA
Security: ~128 bits | Status: For beyond 2030
Recommended
4096-bit RSA
Security: Higher | Use: Long-term protection, root CAs
Maximum Security
🛡️ Security Foundation
RSA's security relies on the computational difficulty of factoring
large numbers
Easy: Multiply two 1024-bit primes
Hard: Factor the 2048-bit product
Time: Billions of years with classical computers
⚛ Quantum Computing Threat
RSA is vulnerable to Shor's algorithm, which can factor large numbers
efficiently on a quantum computer. Current estimates:
⚠️ Key Security Principles
✓
Keep private keys absolutely secret
✓
Use minimum 2048-bit keys
✓
Rotate keys periodically
✓
Use secure padding schemes (OAEP)
Applications#
RSA is used in X.509 certificates to secure web
browsing. When you see the padlock icon, RSA
is likely protecting your connection.
RSA provides authentication and
non-repudiation. Signers cannot deny their
signatures, and recipients can verify authenticity.
Usage: Code signing, document signing
Protocols like S/MIME and PGP use RSA to
encrypt emails, ensuring only intended
recipients can read them.
Usage: Secure corporate email
SFTP, FTPS, and VPNs use RSA for key
exchange and authentication, protecting data
in transit.
Usage: Enterprise file sharing
Developers digitally sign software to prove
authenticity and integrity. Users can verify
software hasn't been tampered with.
Usage: OS updates, app stores
RSA is computationally intensive.
In practice, RSA encrypts symmetric keys
(like AES), which then encrypt large data
efficiently.
Benefit: Best of both worlds
This week dose have seminar class, which theme is phishing, but teacher didn’t provide seminar material, so no separate seminar article this week.