Foundations of Security Week6 Lecture

Lecture Outline
- Introduction to classical cryptography
- Caesar Cipher, Monoalphabetic Substitution Cipher
- Polyalphabetic Cipher - Vigenère Cipher
- Introduction to symmetric key encryption
- Overview of cryptanalysis and cryptographic attacks
Learning Outcomes
By the end of this lecture, students should be able to:
- Know the various classical cryptographies
- Explain Caesar Cipher, Monoalphabetic Substitution Cipher, Polyalphabetic Cipher
- Perform Brute force Attacks on Caesar Cipher
- Understand the Polyalphabetic Cipher - Vigenère Cipher
- Understand Symmetric key encryption
- Understand cryptanalysis and cryptographic attacks
Classical Cryptographies
Caesar Cipher

The Caesar Cipher is one of the simplest and oldest methods of encryption. It is a type of substitution cipher, where each letter in the plaintext is shifted a certain number of positions down or up the alphabet.
It works by shifting the letters of the alphabet by a fixed number, called the shift key. For example, a shift of 3 would replace ‘A’ with ‘D’, ‘B’ with ‘E’, and so on.

For example, a shift of 3 would replace ‘A’ with ‘D’, ‘B’ with ‘E’, and so on.
Then the algorithm can be expressed as follows. For each plaintext letter , substitute the ciphertext letter :
A shift may be of any amount, so that the general Caesar algorithm is
where takes on a value in the range 1 to 25. The decryption algorithm is simply
Example
What is the shift value or key?
Answer:
All 25 Possible Caesar Cipher Shifts (1-13….)
| Letter | S1 | S2 | S3 | S4 | S5 | S6 | S7 | S8 | S9 | S10 | S11 | S12 | S13 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| A | B | C | D | E | F | G | H | I | J | K | L | M | N |
| B | C | D | E | F | G | H | I | J | K | L | M | N | O |
| C | D | E | F | G | H | I | J | K | L | M | N | O | P |
| D | E | F | G | H | I | J | K | L | M | N | O | P | Q |
| E | F | G | H | I | J | K | L | M | N | O | P | Q | R |
| F | G | H | I | J | K | L | M | N | O | P | Q | R | S |
| G | H | I | J | K | L | M | N | O | P | Q | R | S | T |
| H | I | J | K | L | M | N | O | P | Q | R | S | T | U |
| I | J | K | L | M | N | O | P | Q | R | S | T | U | V |
| J | K | L | M | N | O | P | Q | R | S | T | U | V | W |
| K | L | M | N | O | P | Q | R | S | T | U | V | W | X |
| L | M | N | O | P | Q | R | S | T | U | V | W | X | Y |
| M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z |
Brute Force Attack on the Caesar Cipher
Applicability:
Known Algorithms: Encryption and decryption processes are known.
Limited Keys: Only 25 possible keys to attempt.
Recognizable Language: The plaintext language is easily identifiable.
Decryption Example:
Encrypted Message: PHHW PH DIWHU WKH WRJD SDUWB
Decryption Attempts:
An attacker can try all 25 possible keys/shifts in seconds. With modern computers, this takes milliseconds.
Encrypted Message: PHHW PH DIWHU WKH WRJD SDUWB
Decryption Attempts:
| KEY | PHHW | PH | DIWHU | WKH | WRJD | SDUWB |
|---|---|---|---|---|---|---|
| 1 | oggv | og | chvgt | vjg | vqic | rctva |
| 2 | nffu | nf | bgufs | uif | uphb | qbsuz |
| 3 | meet | me | after | the | toga | party |
| 4 | ldds | ld | zesdq | sgd | snfz | ozqsx |
| 5 | kccr | kc | ydrcp | rfc | rmey | nyprw |
| 6 | jbbq | jb | xcqbo | qeb | qldx | mxoqv |
| 7 | iaap | ia | wbpan | pda | pkcw | lwnpu |
| 8 | hzzo | hz | vaozm | ocz | ojbv | kvmot |
| 9 | gyyn | gy | uznyl | nby | niau | julns |
| 10 | fxxm | fx | tvmxk | max | mhzt | itkmr |
| 11 | ewwl | ew | sxlwj | lzw | lgys | hsjlq |
| 12 | dvvk | dv | rwkvi | kyv | kfxr | grikp |
| 13 | cuuj | cu | qvjuh | jxu | jewq | fqhjo |
| KEY | PHHW | PH | DIWHU | WKH | WRJD | SDUWB |
|---|---|---|---|---|---|---|
| 14 | btti | bt | puitg | iwt | idvp | epgin |
| 15 | assh | as | othsf | hvs | hcuo | dofhm |
| 16 | zrrg | zr | nsgre | gur | gbtn | cnegl |
| 17 | yqqf | yq | mrfqd | ftq | fasm | bmdfk |
| 18 | xppe | xp | lqepc | esp | ezrl | alcej |
| 19 | wood | wo | kpdob | dro | dyqk | zkbdi |
| 20 | vnnc | vn | jocna | cqn | cxpj | yjach |
| 21 | ummb | um | inbmz | bpm | bwoi | xizbg |
| 22 | tlla | tl | hmaly | aol | avnh | whyaf |
| 23 | skkz | sk | glzkx | znk | zumg | vgxze |
| 24 | rjjy | rj | fkyjw | ymj | ytlf | ufwyd |
| 25 | qiix | qi | ejxiv | xli | xske | tevxc |
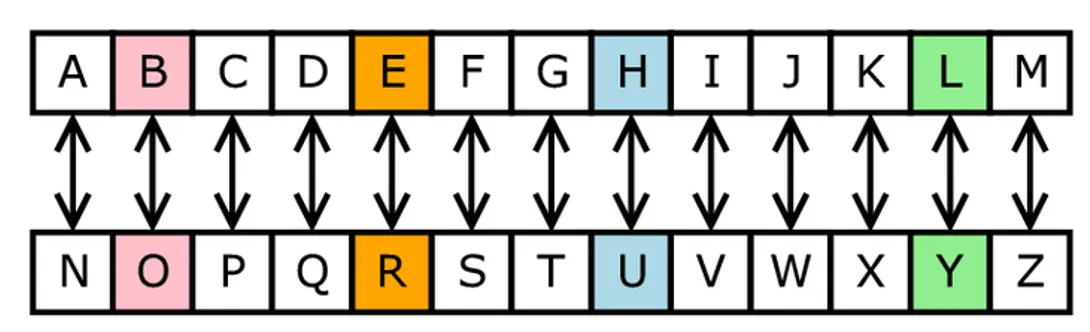
Monoalphabetic Substitution Cipher
Is a type of substitution cipher in which each letter of the plaintext is replaced by a unique letter of the alphabet. This means that a single letter of the plaintext is always substituted by the same letter of ciphertext, and the same substitution is used throughout the message.
Key Characteristics
- One-to-One Mapping: Each letter in the plaintext corresponds to exactly one letter in the ciphertext, and vice versa. For example, ‘A’ might be replaced with ‘D’, ‘B’ with ‘Q’, and so on.
- Fixed Substitution: The substitution pattern remains the same throughout the entire message. If a letter ‘A’ is replaced with ‘D’ in one part of the message, it will be replaced with ‘D’ wherever ‘A’ appears in the plaintext.
- Key: The cipher is defined by a key, which is a permutation of the alphabet. The key determines the substitution of each letter. For example, the key might look like this:
| plain | A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z |
| cipher | Q | W | E | R | T | Y | U | I | O | P | A | S | D | F | G | H | J | K | L | Z | X | C | V | B | N | M |
Encryption Process:
- Step 1: Take the plaintext message.
- Step 2: For each letter in the plaintext, substitute it with the corresponding letter from the ciphertext alphabet according to the key.
- Step 3: The result is the ciphertext, which can be transmitted securely.
Example:
- Plaintext: “HELLO”
- Key (example substitution): A -> Q, B -> W, C -> E, D -> R, E -> T, F -> Y, etc.
- Ciphertext (using the example key): “ITSSG”
- Decryption Process: To decrypt the message, the recipient needs the same key to reverse the substitution, mapping the ciphertext back to the original plaintext.
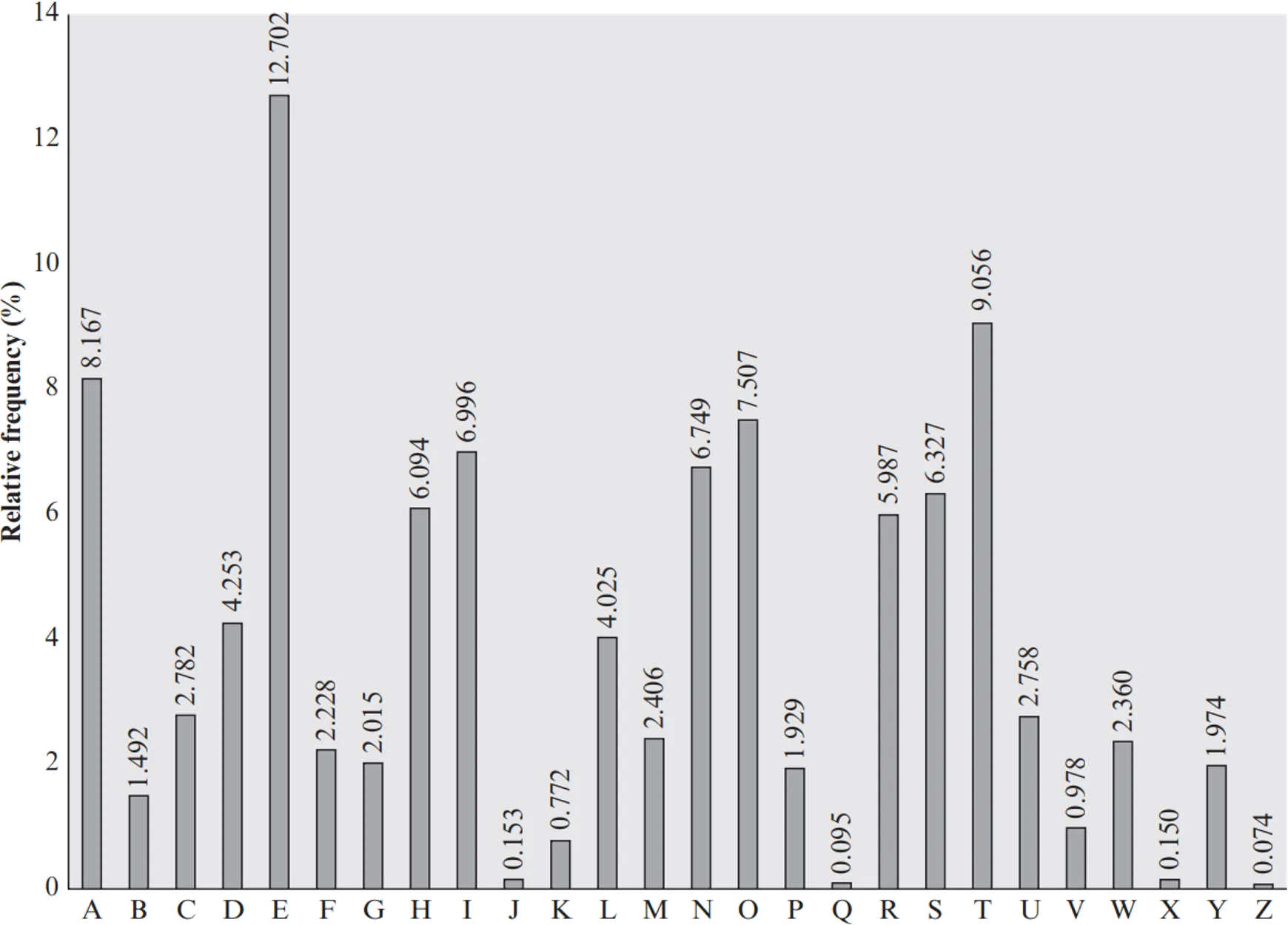
Caesar Cipher
Security:
- Weaknesses: Monoalphabetic substitution ciphers are vulnerable to frequency analysis. In any language, certain letters appear more frequently than others (e.g., ‘E’ is the most common letter in English). By analyzing the frequency of letters in the ciphertext, an attacker can often deduce the substitutions and break the cipher.
- Strengthening: To enhance security, a polyalphabetic cipher, like the Vigenère cipher, can be used, where each letter is substituted based on a changing key, making frequency analysis more difficult.
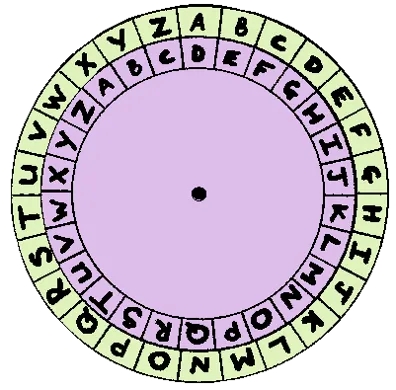
Polyalphabetic Cipher - Vigenère Cipher
Polyalphabetic Cipher
Is a type of substitution cipher that uses multiple substitutions to encrypt a message, unlike the monoalphabetic cipher, which only uses one.
In this cipher, the same letter of the plaintext can be encrypted to different ciphertext letters, depending on its position in the text or a key.
Key Characteristics
- Multiple Substitutions: Instead of using a single substitution for all letters, multiple substitutions are used for the same letter. This makes it harder for attackers to use frequency analysis to break the code.
- Key: The key in a polyalphabetic cipher is typically a word or phrase that is repeated as necessary to cover the entire plaintext. The key determines the shift or substitution for each letter in the plaintext.
- Shift Pattern: Each letter in the key corresponds to a specific shift in the alphabet. For example, if the key is “KEY”, each letter of the plaintext is shifted by the position of the corresponding letter in the key.
Vigenère Cipher
Created by the French diplomat Blaise de Vigenère in the 16th century.
It uses a keyword or key to generate a series of Caesar ciphers based on the letters of the keyword.
Key Characteristics
- Key: The key is a word or phrase that is repeated to match the length of the plaintext.
- Shifting Mechanism: Each letter in the plaintext is shifted by the position of the corresponding letter in the key. The alphabet is shifted forward for each corresponding letter in the key, making the shifts depend on both the letter and its position.
Encryption Process:
- Repeat the key to match the length of the plaintext.
- Shift each plaintext letter forward by the number of positions corresponding to the letter in the key (using the standard alphabetical index, where A = 0, B = 1, C = 2, …, Z = 25).
| A | B | C | D | E | F | G | H | I | J | K | L | M | N | O | P | Q | R | S | T | U | V | W | X | Y | Z |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0 | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | 9 | 10 | 11 | 12 | 13 | 14 | 15 | 16 | 17 | 18 | 19 | 20 | 21 | 22 | 23 | 24 | 25 |
- Example: Encrypt the message “HELLO” using the key “KEY”
- Step 1: Repeat the key to match the length of the plaintext: KEYKE
- Step 2: Encrypt each letter of the plaintext:
| 'H' (shifted by 'K' = 10th letter) -> 'R' | H(7) + K(10) = R(17) mod 26 |
| 'E' (shifted by 'E' = 4th letter) -> 'I' | E(4) + E(4) = I(8) mod 26 |
| 'L' (shifted by 'Y' = 24th letter) -> 'J' | L(11) + Y(24) = J(35) mod 26 |
| 'L' (shifted by 'K' = 10th letter) -> 'V' | L(11) + K(10) = V(21) mod 26 |
| 'O' (shifted by 'E' = 4th letter) -> 'S' | O(14) + E(4) = S(18) mod 26 |
Ciphertext: “RIJVS”
Decryption Process:
-
To decrypt, the receiver uses the same key to reverse the shifting process. Each letter in the ciphertext is shifted backward by the number of positions corresponding to the key letter.
-
Example:
- ‘R’ (shifted back by ‘K’ = 10th letter) -> ‘H’
- ‘I’ (shifted back by ‘E’ = 4th letter) -> ‘E’
- ‘J’ (shifted back by ‘Y’ = 24th letter) -> ‘L’
- ‘V’ (shifted back by ‘K’ = 10th letter) -> ‘L’
- ‘S’ (shifted back by ‘E’ = 4th letter) -> ‘O’
Plaintext: “HELLO”
- Another Example:
Key: deceptivedeceptivedeceptive
Plaintext: wearediscoveredsaveyourself
ciphertext: zicvtwqngrzgvtwavzhcqyglmgj
| key | 3 | 4 | 2 | 4 | 15 | 19 | 8 | 21 | 4 | 3 | 4 | 2 | 4 | 15 |
| plaintext | 22 | 4 | 0 | 17 | 4 | 3 | 8 | 18 | 2 | 14 | 21 | 4 | 17 | 4 |
| ciphertext | 25 | 8 | 2 | 21 | 19 | 22 | 16 | 13 | 6 | 17 | 25 | 6 | 21 | 19 |
| key | 19 | 8 | 21 | 4 | 3 | 4 | 2 | 4 | 15 | 19 | 8 | 21 | 4 |
| plaintext | 3 | 18 | 0 | 21 | 4 | 24 | 14 | 20 | 17 | 18 | 4 | 11 | 5 |
| ciphertext | 22 | 0 | 21 | 25 | 7 | 2 | 16 | 24 | 6 | 11 | 12 | 6 | 9 |
A general equation of the encryption process is
Similarly, decryption is a generalization of the form
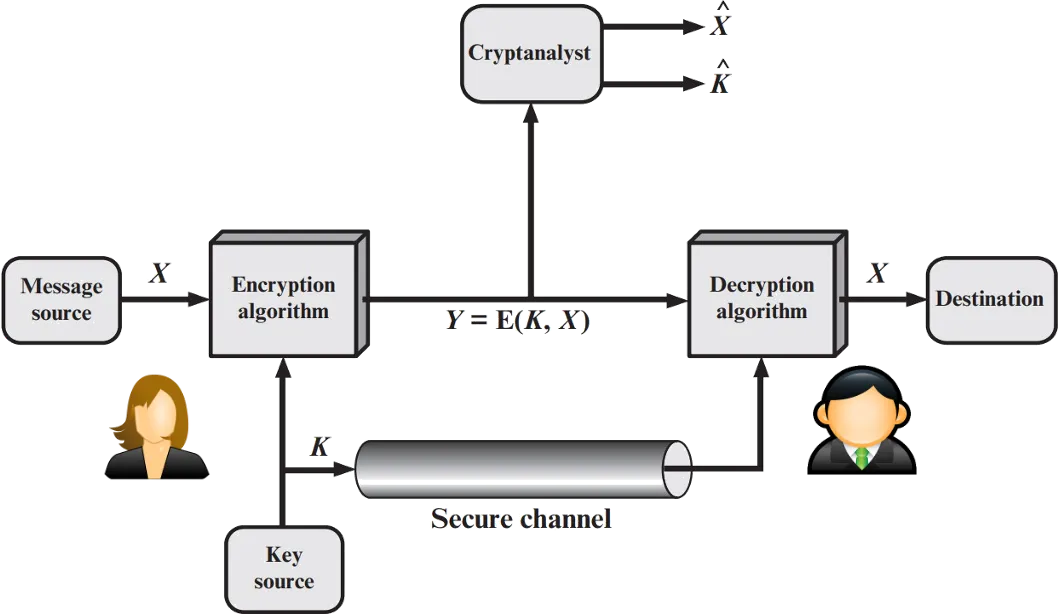
Symmetric Key Encryption
Symmetric Key Encryption is a cryptographic method where the same key is used for both encryption and decryption.
In this system, both the sender and the receiver share a secret key, and they use it to transform plaintext (original message) into ciphertext (encrypted message) and vice versa.
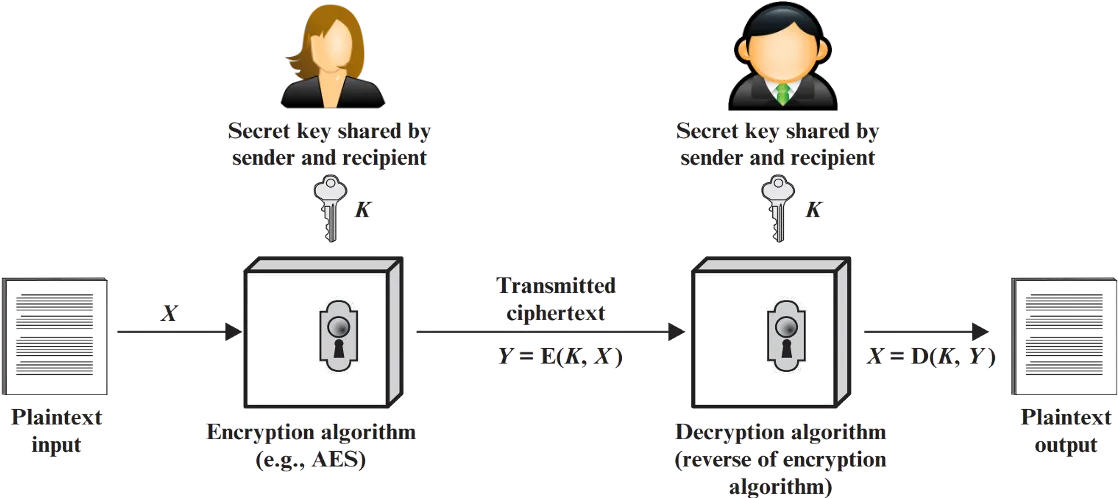
Key Characteristics
Single Shared Key:
The key used for encryption and decryption is the same, which is why it is called “symmetric.” Both the sender and receiver must securely share and protect the key.
Encryption and Decryption Process:
- Encryption: The plaintext is transformed into ciphertext using an encryption algorithm and the shared secret key.
- Decryption: The ciphertext is transformed back into plaintext using the same algorithm and key.
Confidentiality:
The security of the system relies on keeping the key secret. If an attacker gains access to the key, they can easily decrypt the message.
Efficiency:
They are generally faster and more efficient than asymmetric key encryption algorithms, making them suitable for encrypting large amounts of data.
They use less computational power and resources compared to asymmetric encryption
Cryptanalysis Attacks
Cryptanalysis is the study of methods for breaking or undermining the security of cryptographic systems. It involves trying to decipher ciphertext without access to the secret key, in order to retrieve the plaintext or gain other useful information.
Reading Assignment
Read on the below 4 cryptanalysis attacks
Extended reading: https://ctf-wiki.org/crypto/classical/monoalphabetic/
支持与分享
如果这篇文章对你有帮助,欢迎分享给更多人或赞助支持!
